Insecure QR codes on COVID-19 test results come with data exposure risks
Medical labs appointed by governments to test incoming international passengers for COVID-19 contain insecure QR code implementations that may lead to data exposure.
As more and more governments around the world impose mandatory coronavirus testing for arriving international passengers during the ever-evolving pandemic situation, the increased pressure has led to rushed and buggy implementations of systems that provide COVID-19 test results online.
In at least one such case, discovered and responsibly reported by Security Report, COVID-19 test results for an uncountable number of arriving passengers and patients who underwent a government-mandated coronavirus test were vulnerable to online data leaks due to a simplistic implementation flaw in an online system lacking adequate security controls.
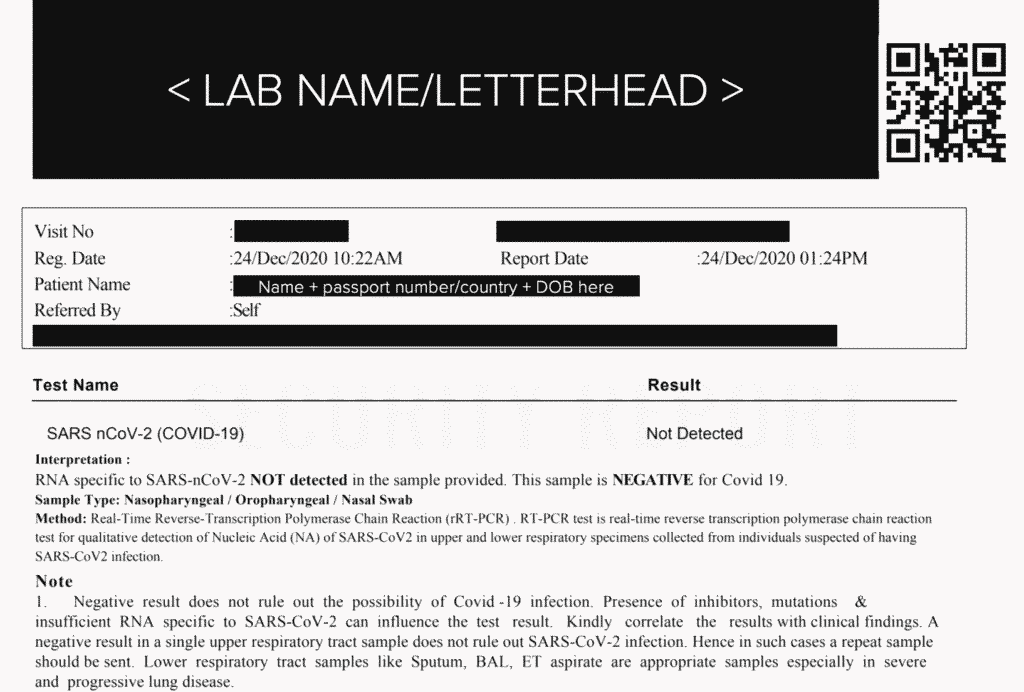
Among the exposed data, we noticed the electronic reports exposed the patient’s full name, date of birth, passport number, nationality (country that issued the passport), date of COVID-19 test, and test result (positive, negative, inconclusive, etc.).
Insecure QR code implementation
The flaw had occurred because every paper copy of COVID-19 test results contained a QR code which led to its electronic version.
Surprisingly, the URL to this electronic copy had a rather simple structure:
http://[server address]/Path/to/report/viewreport.aspx?VisitNumber=MTIzNDU2Nw==
The GET URL parameter Visit Number or Lab Test Number (and other variations of the serial number field observed in the URL that the QR code led to) is a simply base64-encoded representation of “serial number” associated with a lab report.
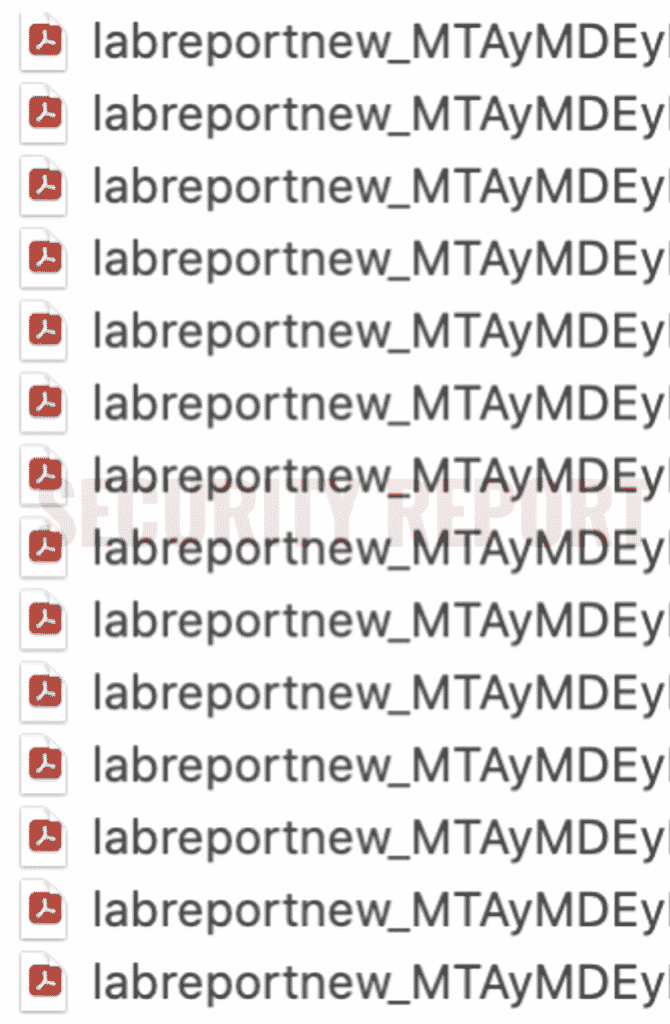
By trivially decoding the base64 value present in the URL, incrementing/decrementing or changing the serial number of the report to an arbitrary value, and re-encoding it to base64, an attacker could enumerate and access other patients’ COVID-19 test reports.
In our tests, by following this workflow, Security Report could access well over 30 COVID-19 lab reports of different patients, at which point, we stopped our tests and began with the responsible disclosure of the flaw.
Test labs share a common software vendor
On noticing the flaw, Security Report immediately notified the affected hospitals and labs, some of which have patched the flaw within hours of our report—by disabling the QR code (lab report) URLs altogether.
On further investigation, we noticed the hospitals and labs issuing lab reports that look like the one shown above shared a common software vendor. This vendor serves prominent hospitals and labs across India, Mauritius, Ghana, Nepal, Congo, and Tanzania.
Security Report has additionally reached out to the software vendor to correct this issue for any other medical clients that may be vulnerable.
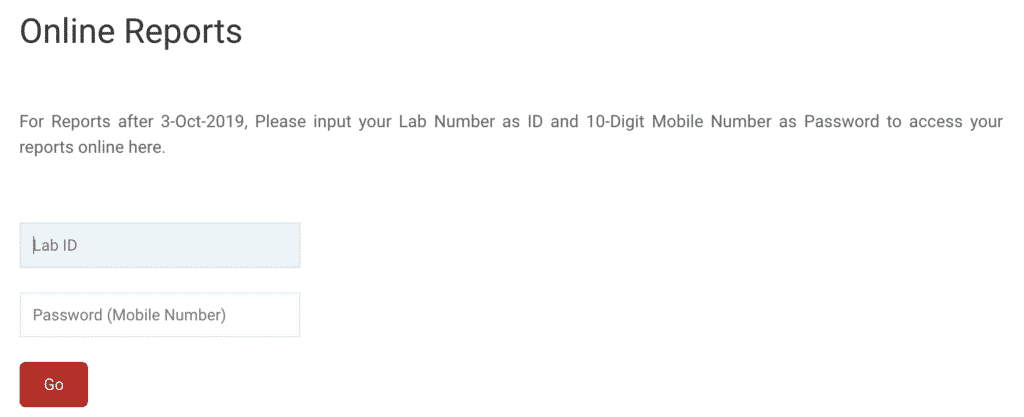
Some of the hospitals are using an additional password field such as the user’s mobile phone number, which would prevent an attacker from simply guessing and enumerating lab report serial numbers sequentially. and obtaining lab test reports for virtually any patient via crafted URLs.
The same system is also being used by healthcare facilities to provide online lab reports for other lab tests (e.g. abdomen CT scans) which aren’t limited to just COVID-19 results. Therefore, it is likely, up until this point these systems were exposing any and all lab reports for every patient in an effort to provide “easy online access.”
As a rule, if web access is desired for confidential files, such as medical records, these should be password protected or have some other security controls in place.
Providing access to such files via QR codes containing a static publicly accessible URL should be carefully evaluated.
At a minimum, such URLs should contain randomly-generated, hard to guess fields (much like a password) in addition to the document’s serial number. The serial should itself be represented as a hash or an alphanumerical identifier, rather than a straightforward numerical ID. Following these tips will make it very difficult for a casual attacker to “guess” and enumerate publicly accessible links.
For example, every test report URL embedded in the QR code could look like:
http://[server address]/Path/to/report/viewreport.aspx?VisitNumber=1234567&securitycode=2cf3ddc3762d3020b4aef02114239c55
or even use a randomized alphanumberical string as the visit or lab report ID:
http://[server address]/Path/to/report/viewreport.aspx?VisitNumber=b59dn120491&securitycode=2cf3ddc3762d3020b4aef02114239c55
The MD5 hash can be based on the combination of a server-sided secret (unknown to the patient or anyone) and maybe the visit number field. There are multiple ways of accomplishing this, but the end goal is to make it impossible for an attacker to guess public URLs that lead to confidential documents.
Additionally, the system administrator should ensure online web systems providing access to medical records and lab reports are not crawled and indexed by search engines like Google. This is where robots.txt comes in handy.


