New convincing phishing campaign targets Booking.com and Blockchain.com customers
New series of convincing phishing emails use Fleek.co’s infrastructure to collect credentials.

Photo by Pixabay on <a href="https://www.pexels.com/photo/brown-hut-island-gazebo-38238/" rel="nofollow">Pexels.com</a>
A new series of convincing phishing emails analyzed by Security Report are designed to impersonate Booking.com, but go a step further.
These emails titled “Action needed: You have Virtual Credit Cards to refund.” appear to be originating from Booking.com, with their ‘From’ email address forged to state noreply@booking.com.
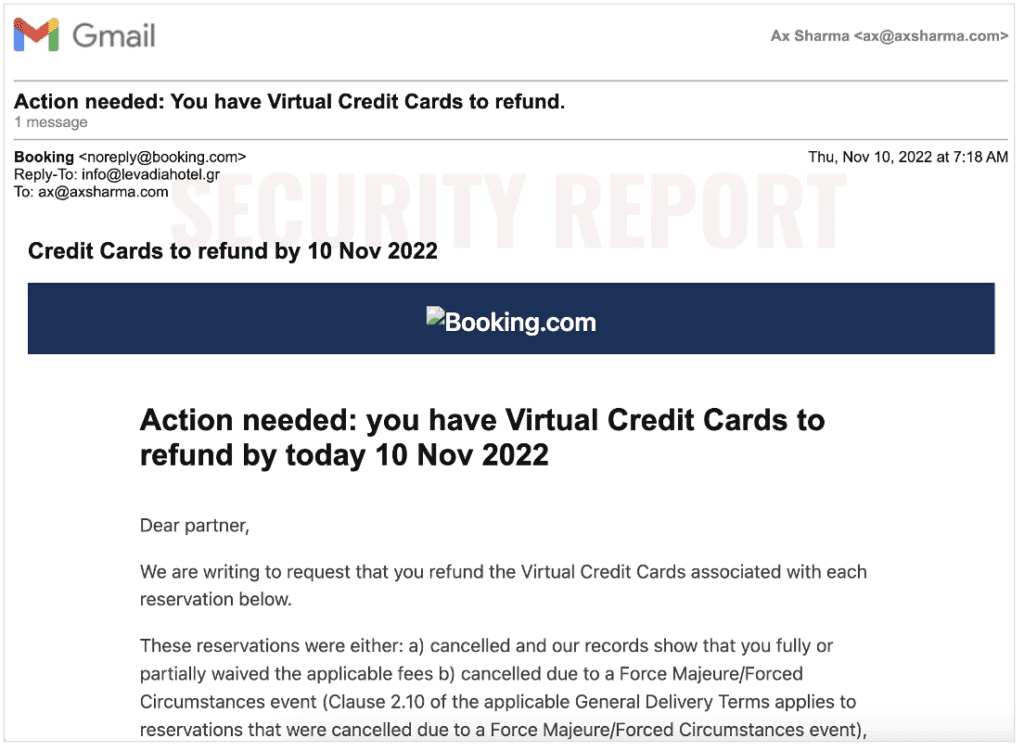
To make it seem more convincing, the Reply-To is set to info@levadiahotel.gr which is the contact email of a real property, Levadia Hotel, Greece.
While spoofing the ‘Envelope From’ or ‘Mail From‘ address field is hardly new, and a commonly seen phishing tactic, the wording of the message lends some credibility to its contents.
The phishing message urges the “partner,” supposedly a property owner using Booking.com to rent their hotel or apartment, to “refund the Virtual Credit Cards associated with each reservation below.”
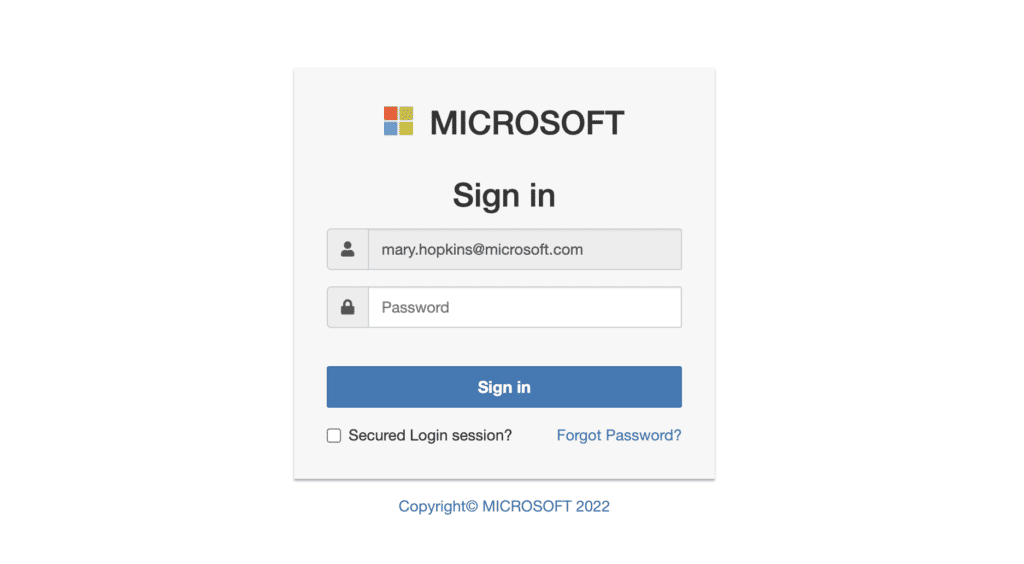
The phishing link at least leads to a pretty simplistic form hosted on Fleek.co’s infrastructure.
An example phishing page (archived) found linked within such emails is shown below:
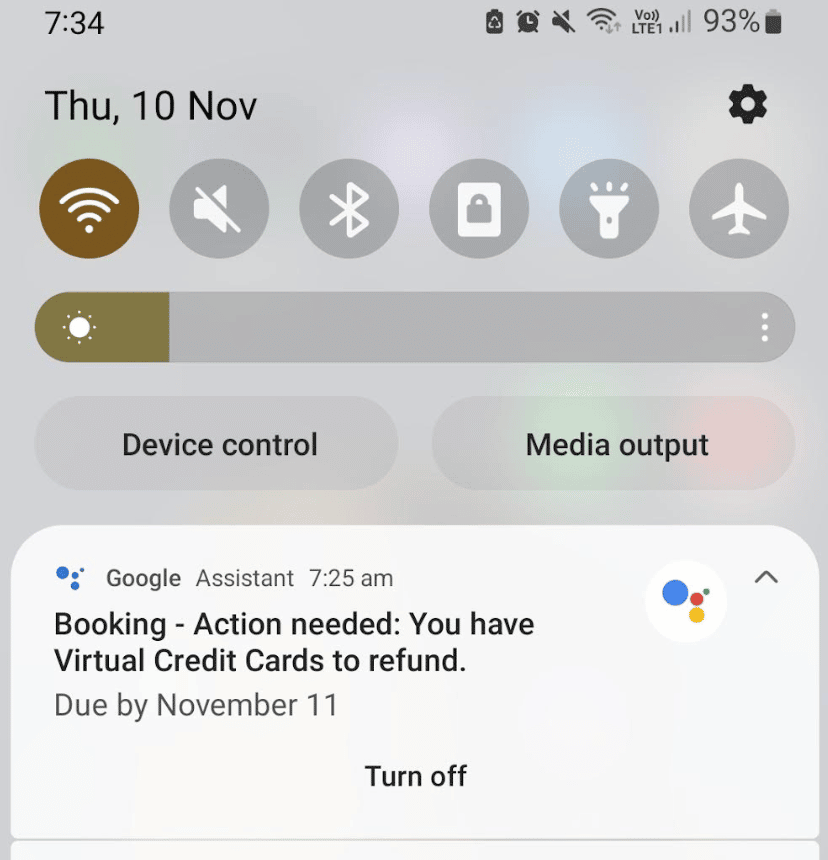
Interestingly, Google Calendar app may automatically pick spammy emails arriving in your Gmail and add these to your calendar, unless your calendar settings are set appropriately to prevent this.
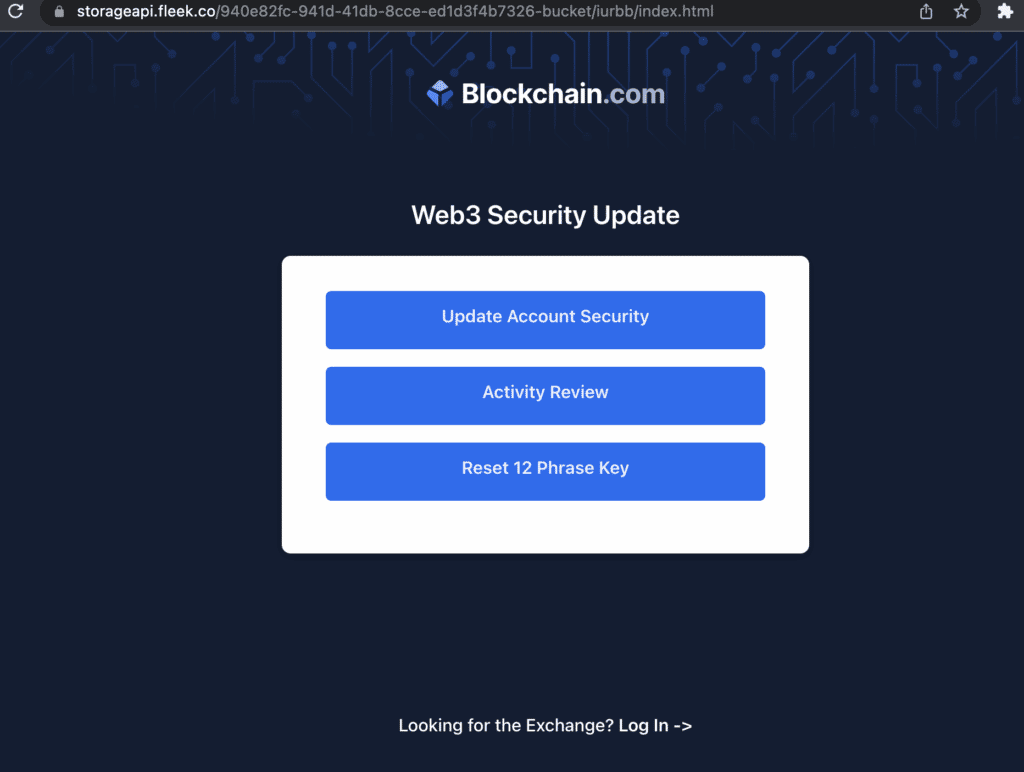
An identical phishing message emerged, this time appearing to originate from ‘Blockchain.com’ and once again using a spoofed ‘From’ email field.
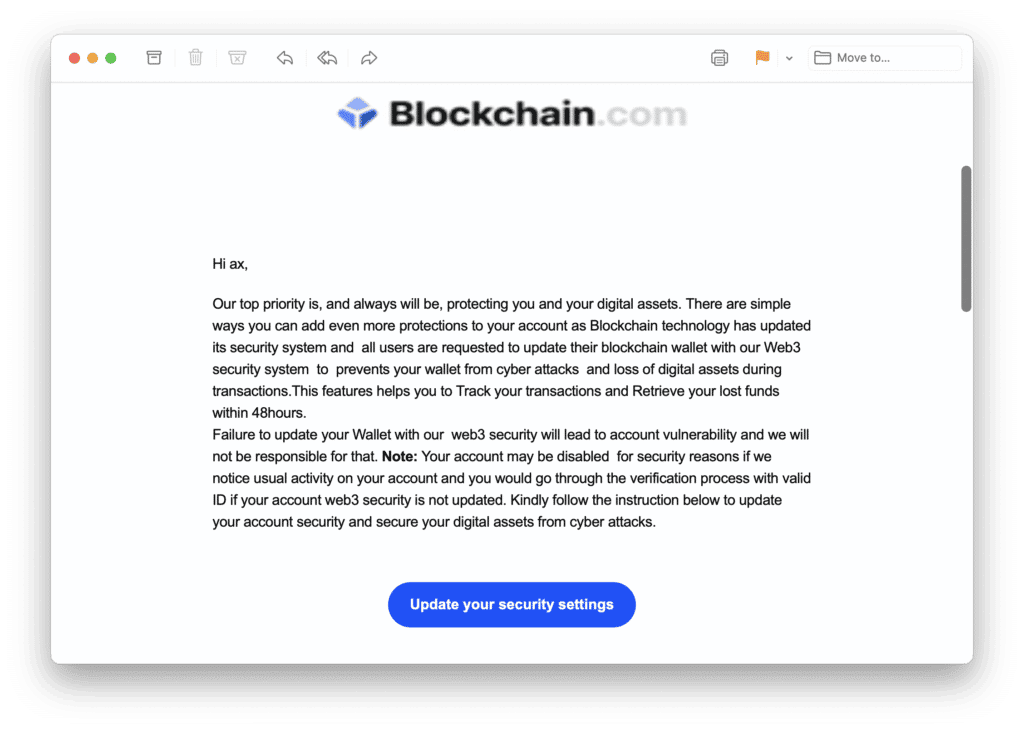
The ‘Update your security settings’ button once again leads to a simplistic phishing form, also hosted on Fleek.co’s server, collecting your credentials.
Security Report notified fleek.co of these emails and the suspicious links prior to publishing.
These phishing messages surface at a time when threat actors are targeting Twitter users with the introduction of the platform’s new $8 fee for the “Twitter Blue” experience and verification.
In other instances, convincing phishing scams have led to major compromises including that of Dropbox’s 130 GitHub repositories after a successful phishing attack that targeted Dropbox employees.
As always, users should remain careful when it comes to clicking links or attachments in emails that appear even slightly suspicious.


