Phishing kit screenshots your email domain on the fly to appear real
Phishing kit used by multiple hacked sites generates a log in page on the fly that closely resembles the victim’s email domain.

Photo by Kaique Rocha on <a href="https://www.pexels.com/photo/man-holding-camera-while-squating-with-smoke-on-face-inside-building-598917/" rel="nofollow">Pexels.com</a>
In a phishing campaign analysed by Security Report this week, threat actors are deploying JavaScript code within phishing webpages to generate the page’s background based on the domain associated with victim’s email address.
This means, the phishing kit can be repurposed dynamically, across any number of domains as the need to manually imitate the website design by threat actors is now eliminated. A threat actor can, for example, use the same phishing URL to phish victim email addresses registered to virtually any domain.
On demand phishing page generation
One of the phishing messages analysed in this campaign is shown below. The email falsely claims to the recipient that incoming email messages are being quarantined and the issue must be “resolved.”
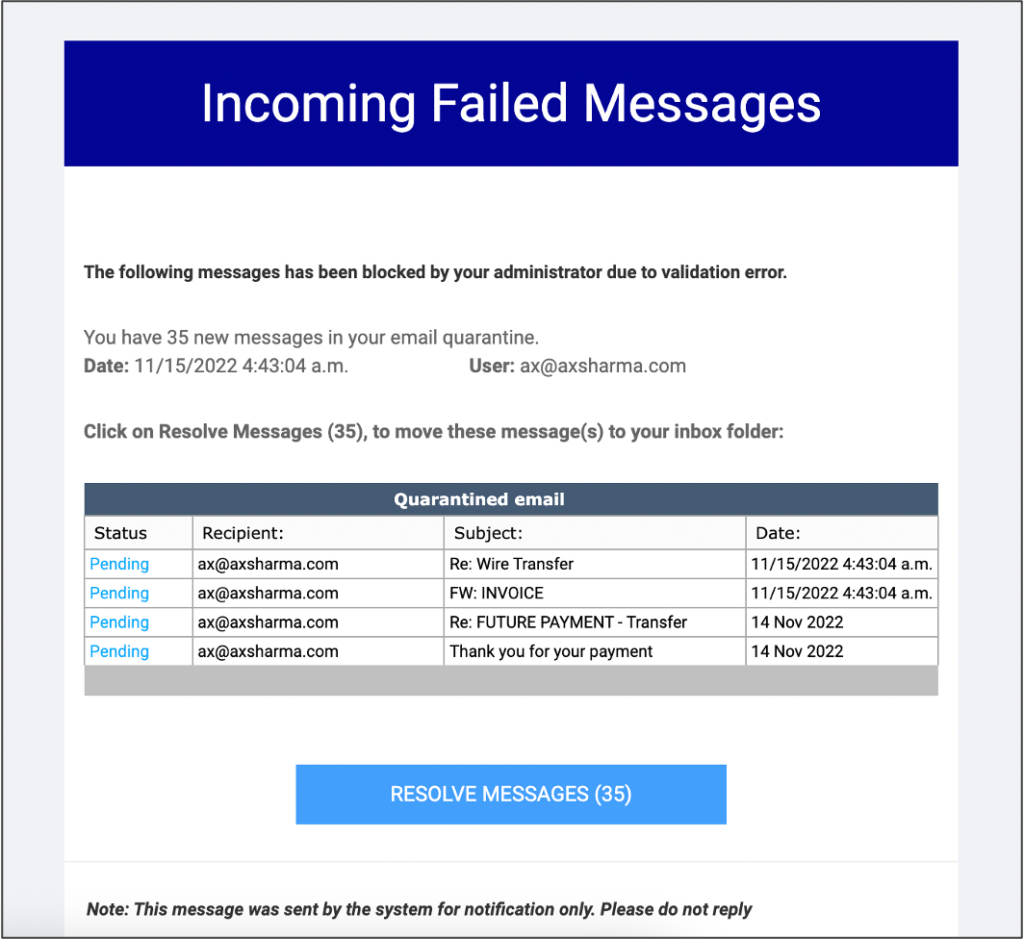
Clicking on the “Resolve Messages…” link leads you to a phishing webpage, URL for which contains the email address that the phishing message was sent to.
For example, if your email address is test@microsoft.com and this is where the phishing email had arrived, the URL to phishing webpage would contain that email address. And both the logo for the phishing form and the background are generated based on the domain “microsoft.com” on the fly:
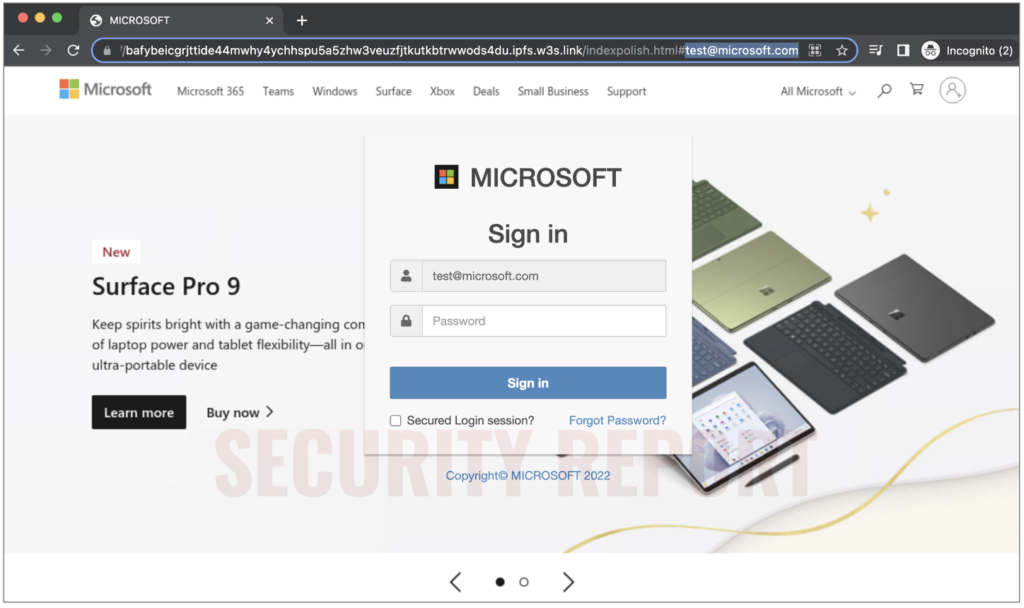
But, had the email arrived at say your-email@gmail.com, the form logo and webpage background would now be automatically changed to reflect Google’s look and feel.
In another test below, we switched the test@microsoft.com email address to victim@amazon.co.uk. Notice the background and phishing form logo change.
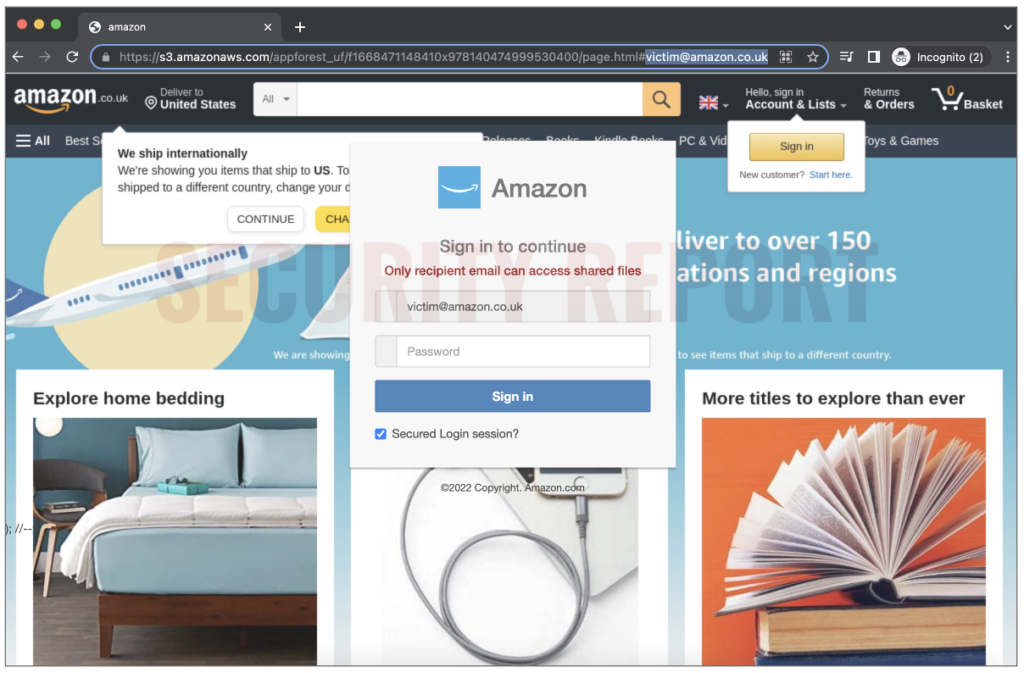
As evident from the screenshots above, the campaign is using Amazon AWS and web3.storage to host phishing webpages.
Logobit and Thum.io used for generating graphics
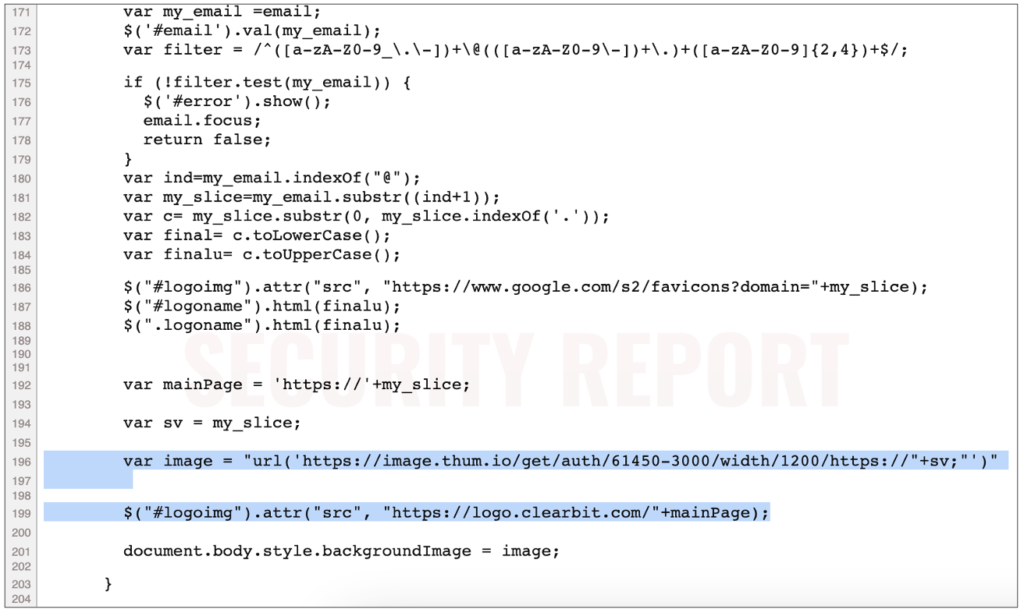
The client-side code seen by Security Report in the phishing pages indicates it is using Thum.io, a website screenshot generator service to generate the page background—based on the domain of the victim’s email address.
Further, Clearbit is used for fetching the appropriate logo image for the webform.
August this year, LA-based cybersecurity firm Resecurity analysed a phishing kit dubbed LogoKit that also made use of Clearbit to fetch the company logo.
“LogoKit relies on sending users phishing links that contain their email addresses. Once the victim navigates to the URL, LogoKit fetches the company logo from a third-party service, such as Clearbit or Google’s favicon database,” explained Resecurity researchers.
“LogoKit is known for its dynamic content generation using JavaScript – it is able to change logos (of the impersonated service) and text on the landing pages in real-time to adapt on the fly, by doing so the targeted victims are more likely to interact with the malicious resource. Around November 2021, there were over 700 identified domains names used in campaigns leveraging LogoKit – their number is constantly growing.”
The phishing campaign observed by us this week takes LogoKit’s tactics a step further but combining these with dynamic background image generation based on the target victim’s domain.
As always, it’s a good practice to be wary of emails you receive, and to refrain from opening suspicious links or attachments within them.


