Hacker selling Vodafone’s Ho Mobile database of 2.5M users
The database contains ICCID that can be used in SIM swapping attacks. Other information in the leaked dump includes mobile number, customer PII, SIM PUK, IMSI and security hashes.
A threat actor has posted a thread on one of the dark web forums claiming to sell Ho Mobile’s database of 2,500,000 users, as observed by Security Report.
Ho Mobile is an Italian telecom carrier owned by Vodafone.
This week threat analyst Bank Security first shared details related to the post on Twitter, after which Security Report analyzed the data sample posted in the forum.
While there is nothing confirming yet if this data is authentic and belongs to Ho Mobile, as observed by Security Report, the leaked data sample of 10 customers posted by threat actor LongPig includes:
- Customer’s PII: name, date of birth, address, email, mobile number, etc.
- SIM card PUK code
- ICCID number
- IMSI number
- Various base64-encoded hashes
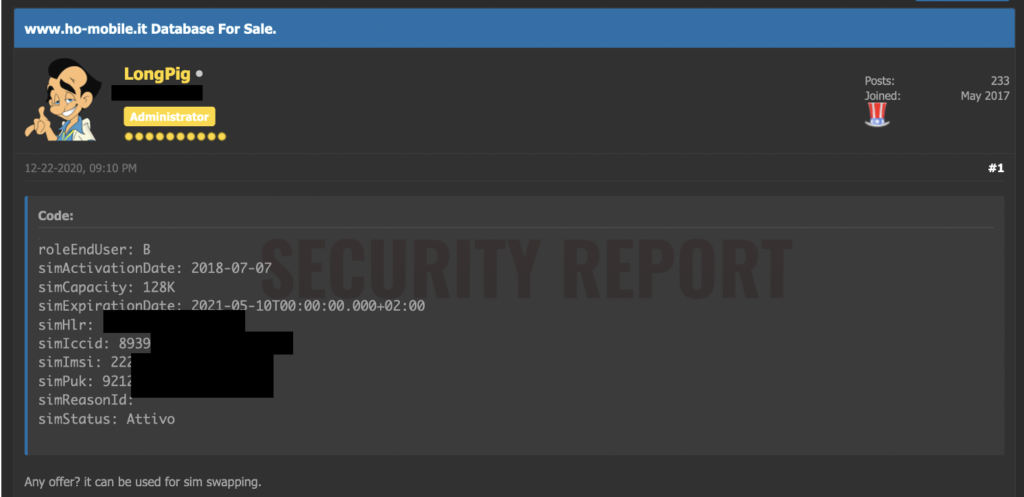
This information can be abused by threat actors in SIM swapping attacks to effectively take control of the phone number.
Consequently, attacks may be able to bypass SMS-based 2FA (two-factor authentication) security employed by banking websites, email, and security-centric online systems and potentially breach customer accounts on these websites.
Another forum user responded to LongPig’s post snarkily commenting:
Probably not worth much after KE-LA, IB-Group, and whatever other extra-chromosome baring collective (security firm) sees thisTo this, LongPig rebutted with, “all data is already dumped and to sim swap you require only phone number and the ICCID so it will still works unless they send new SIMs card to all 2,5M customers.”

Vodafone or Ho Mobile have not yet confirmed if this data is authentic. Should that be the case indeed, it might be very difficult for the telecom carrier to safeguard customers against SIM swap attacks originating from this leak, as the threat actor says, without reissuing the SIM cards.
Security Report has reached out to Vodafone and Ho Mobile and we are awaiting a response.
Update 29-Dec-2020:
While calling the threat actor’s claims “rumors,” Ho Mobile has told us that they are currently investigating the case:
“With reference to some rumors published by the press, ho.mobile has no evidence of massive access to its IT systems that have jeopardized the data of the customer base.”
“We have started investigations in collaboration with the investigative authorities for further investigations. We remain at your disposal,” a Ho Mobile spokesperson told Security Report.
Update 30-Dec-2020:
However, not everyone is convinced, as a supposed API that would return Ho Mobile users’ information seems to have existed since at least 2019.
Update 4-Jan-2021:
After previously dismissing reports of the data breach as “rumours,” Ho Mobile has now admitted to the data breach in a notice issued today.
https://www.ho-mobile.it/comunicazione/
Thanks to Bank_Security for the initial tip off and for providing updates throughout this developing story.


