Joomla fixes ACL violation vulnerability after 2 years
Joomla! CMS project has fixed an access control violation flaw, CVE-2020-35616 nearly after 2 years of its reporting.

The development team behind popular CMS Joomla which powers over 2.5 million sites has patched an access control violation vulnerability this week.
Tracked as CVE-2020-35616, the vulnerability is an input validation flaw when checking permissions that can allow users to bypass rules set by Access Control Lists (ACLs).
“Lack of input validation while handling ACL rulesets can cause write ACL violations,” states the Joomla security advisory.
Although the flaw was reported on 4th November 2018, it was fixed this month by Joomla team on 24th December 2020.
Rohan Sharma, a security researcher from SecureLayer7 explained if exploited, this vulnerability could enable attackers (authenticated CMS users) to access areas of Joomla CMS, such as Categories, which are otherwise restricted to certain user groups.
Sharma demonstrated how a Category created by the Manager user and restricted to Administrator could be accessed by the Administrator user by POSTing a crafted payload, shown below, to the CMS:
&jform%5Brules%5D%5Bcore.create%5D%5B7%5D=1&jform%5Brules%5D%5Bcore.delete%5D%5B7%5D=1&jform%5Brules%5D%5Bcore.edit%5D%5B7%5D=1&jform%5Brules%5D%5Bcore.edit.state%5D%5B7%5D=1&jform%5Brules%5D%5Bcore.edit.own%5D%5B7%5D=1The flaw impacts all Joomla CMS versions from 1.7.0 to 3.9.22 (inclusive).
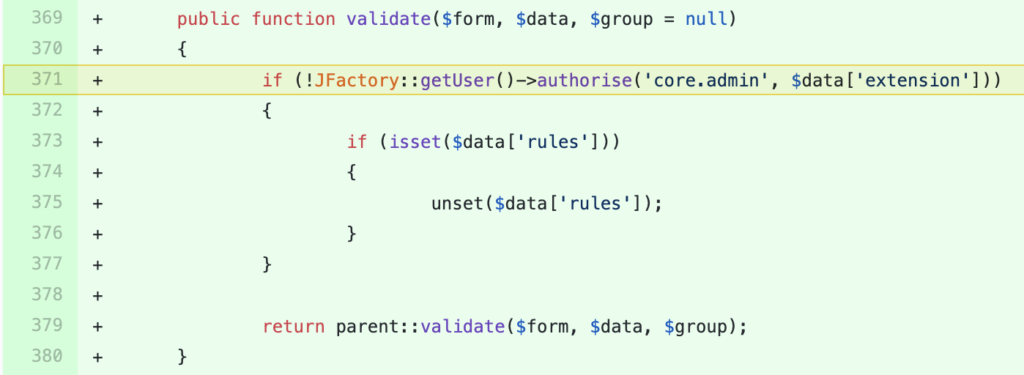
Joomla team has fixed the flaw in version 3.9.23 by adding a validate function that appropriately checks permissions, as shown below.
Users of Joomla CMS are encouraged to upgrade their installations to fixed version(s) 3.9.23 and above.
A PoC video demonstrating the exploit for CVE-2020-35616 has been provided by SecureLayer7:
Although the flaw, if exploited, has a High impact considering restricted resources can be accessed by users which were otherwise not supposed to access them, it has been assigned a Low severity rating because the users need to be authenticated.


