Apple SSH privacy bug “exploited at large” remains unpatched after 2 years
A privacy bug lurking around in Apple Mac OS X since at least 2018 continues to remain unpatched and exploited at large.

A privacy bug lurking around in Apple Mac OS X since at least 2018 continues to remain unpatched.
The severity of the bug could be considered moderate, as the attacker would first need to establish an SSH connection to the system. However, it forms one of the Improper Authorization exploits actively leveraged by the XCSSET Mac Malware, described in TrendMicro’s report.
XCSSET malware targets XCode projects, altering them in such a way, that they execute malicious code on building.
In a technical brief PDF provided by TrendMicro, the “Data Vault vulnerability used in Safari cookie theft” specifically refers to this very SSH vulnerability.
The bug was previously discovered and reported by Howard Oakley in his blog post titled “Who put that in my Full Disk Access list?”
In fact, security engineer Mikey (0xmachos) wasted no time in calling out TrendMicro for not referencing Oakley in their report.
Oakley explained how in certain cases, macOS would automatically give ssh Full Disk Access to a connected user, effectively bypassing their privacy settings.

Source: EclecticLight blog
Typically, macOS systems are in one of the three states, with regards to SSH access:
- they were never accessed over SSH. Therefore, the
sshd-keygen-wrapperentry is not present in the Full Disk Access list, or - have been accessed over SSH with Full Disk Access permission granted, due to
sshd-keygen-wrapperbeing listed and ticked, or - accessed over SSH but permissions were now removed, with
sshd-keygen-wrapperlisted under Full Disk Access but not ticked.
“It is only when Privacy settings are in the last state that access to protected data will be refused. The only control that the user has is enabling and disabling the sshd-keygen-wrapper in the Full Disk Access list, which has the effect of toggling access to protected data for that user,” stated Oakley in his original blog post.
Moreover, removing the sshd-keygen-wrapper from the Full Disk Access list didn’t prevent access to protected data at all!
This means, ideally when in the first state, macOS should by default prevent granting access to areas specified by “sshd-keygen-wrapper,” should the setting had been ticked. But that isn’t the case.
Unchecking “sshd-keygen-wrapper” from the list is acceptable, and works as intended. But removing it altogether will actually add it back into the list in a “ticked” state.
Consequences? Exploited at large.
This means a user accessing macOS over SSH will now have full permissions and privileges offered as if this option was ticked. This directly concerns the user’s privacy.
“To gain full access to any privacy-protected directory, all an attacker has to do is establish an ssh connection. Provided Remote Login is enabled, and sshd-keygen-wrapper isn’t both present and disabled (unticked) in the Full Disk Access list, macOS will automatically bypass its own privacy protection without any further control,” states Oakley in his latest post.
This behaviour can be exploited by malware and sophisticated “vulnerability chaining” exploits to steal sensitive files, such as Safari browser cookies.
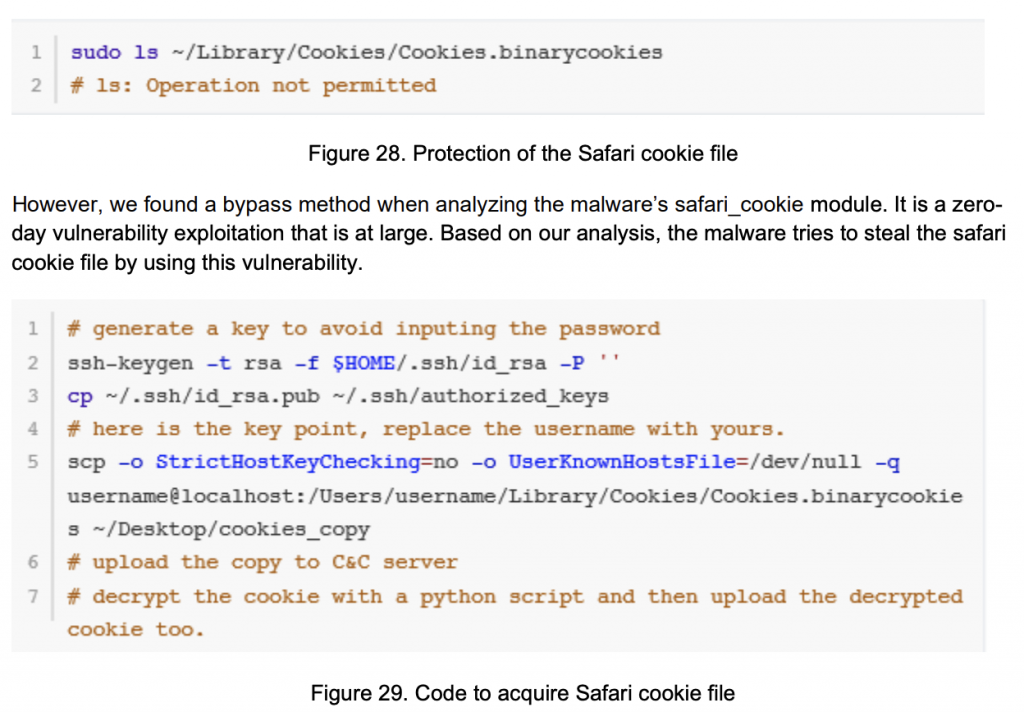
“macOS protects the Safari cookie file ~/Library/Cookies/Cookies.binarycookies with the System Integrity
Protection (SIP) feature. However, we found a bypass method when analyzing the malware’s safari_cookie module. It is a zero-day vulnerability exploitation that is at large,” reads TrendMicro’s technical brief on XCSSET.
Remediating what’s not a “zero-day”
While TrendMicro refers to this vulnerability as a “zero-day,” not all experts agree.
For example, Thomas Reed, Director of Mac and Mobile at Malwarebytes told The Daily Swig:
“The Data Vault vulnerability is definitely not a zero-day, as it’s been known for a couple of years that using SSH/SCP bypasses TCC restrictions. This is a known issue, but it’s been known since 2018 and may, at this point, be something that Apple considers to be working as intended.”
Oakley’s recommendation advice comes in two measures which would make it harder for attackers to exploit this bug:
“Disable Remote Login and ensure that sshd-keygen-wrapper has been added to your Mac’s Full Disk Access list but is unticked there.”
Until Apple patches this privacy omission in their OS X builds, the vulnerability may continue to be exploited as a part of advanced attacks on Apple systems.


