Palo Alto Networks researcher discovers Linux privilege escalation vulnerability

A privilege escalation vulnerability had been lurking in the Linux kernel all this time until being discovered by a Palo Alto Networks researcher last week.
Assigned CVE-2020-14386, the memory corruption flaw can be exploited by a standard user to gain extended permissions as an administrator (root) on Linux systems.
“A flaw was found in the Linux kernel before 5.9-rc4. Memory corruption can be exploited to gain root privileges from unprivileged processes. The highest threat from this vulnerability is to data confidentiality and integrity,” reads the vulnerability’s official NVD description.
Or Cohen of Palo Alto Networks has been credited with discovering the vulnerability.
In a blog post for the company’s Unit42 blog, Cohen stated:
“Specifically, in order for the vulnerability to be triggerable, we need the kernel to have AF_PACKET sockets enabled (CONFIG_PACKET=y) and the CAP_NET_RAW privilege for the triggering process, which can be obtained in an unprivileged user namespace if user namespaces are enabled (`CONFIG_USER_NS=y`) and accessible to unprivileged users.”
“Surprisingly, this long list of constraints is satisfied by default in some distributions, like Ubuntu,” continued Cohen.
According to Cohen, similar vulnerabilities have been reported in the past:
“A few years ago, several vulnerabilities were discovered in packet sockets (CVE-2017-7308 and CVE-2016-8655), and there are some publications, such as this one in the Project Zero blog and this in Openwall, which give some overview of the main functionality,” he said in the post.
However, the fixes previously applied by the project developers did not sufficiently resolve the memory corruption vulnerabilities, which is why Cohen was able to provide a Proof-of-Concept (PoC) exploit to demonstrate the flaw persisted.
A patch proposed by the researcher can be used to resolve the bug:
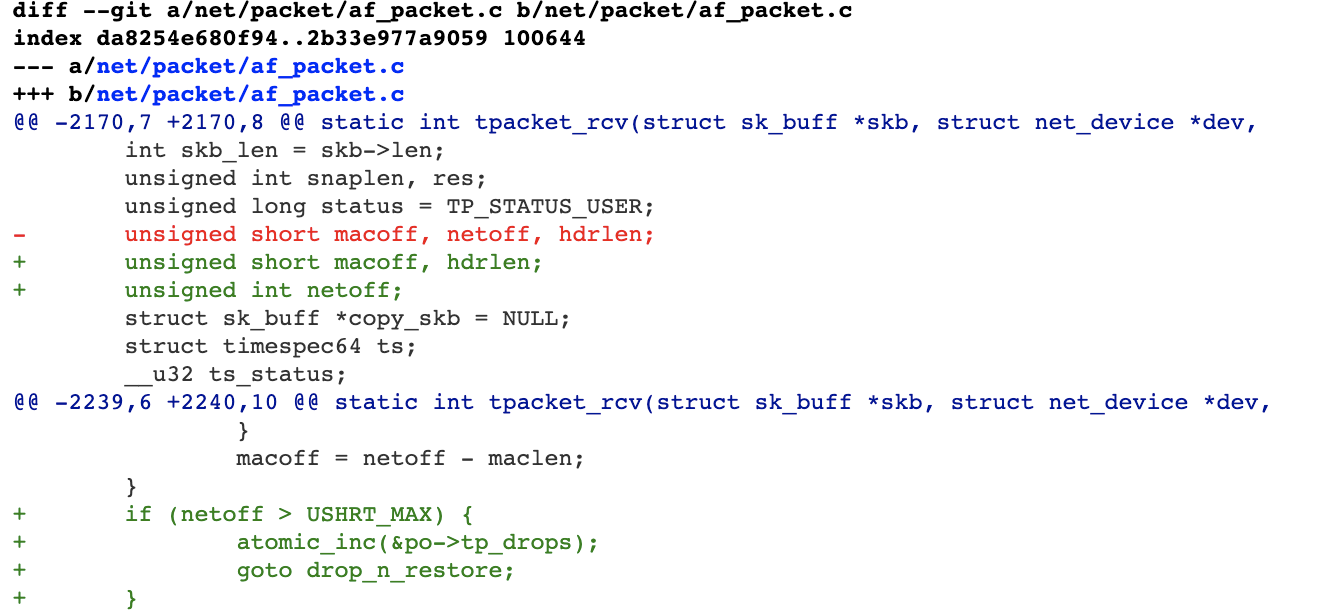
Source: Palo Alto Networks
“I was surprised that such simple arithmetic security issues still exist in the Linux kernel and haven’t been previously discovered,” said Cohen.
“Also, unprivileged user namespaces expose a huge attack surface for local privilege escalation, so distributions should consider whether they should enable them or not,” the researcher concluded.
Cohen’s thorough technical findings are provided in the blog post.


