Backdoor master password for thousands of Zyxel firewalls revealed
Thousands of Zyxel firewalls and access point controllers contain a secret, undocumented hardcoded password giving anyone admin access through this zero-day.
Multiple Zyxel devices including firewalls and access point (AP) controllers contain a hardcoded username-password combination in the firmware images, which has now been revealed.
These credentials stored in plaintext and visible to anyone with access to the firmware image can give them administrator access to the device via SSH, making this a serious zero-day vulnerability.
Zyxel Communications is a Taiwan-based manufacturer of networking devices, with offices around the world. The $379 million company employees over 1,500 people worldwide.
Hardcoded master password exposed in firmware images
Tracked as CVE-2020-29583, the High severity vulnerability concerns cleartext storage of sensitive information within Zyxel device firmware—in this case, hardcoded master password that can give administrator access to anyone via SSH.
According to Zyxel, the original purpose of this undocumented password was to deliver automatic updates to devices via FTP.
“A hardcoded credential vulnerability was identified in the ‘zyfwp‘ user account in some Zyxel firewalls and AP controllers. The account was designed to deliver automatic firmware updates to connected access points through FTP,” states Zyxel’s security advisory.
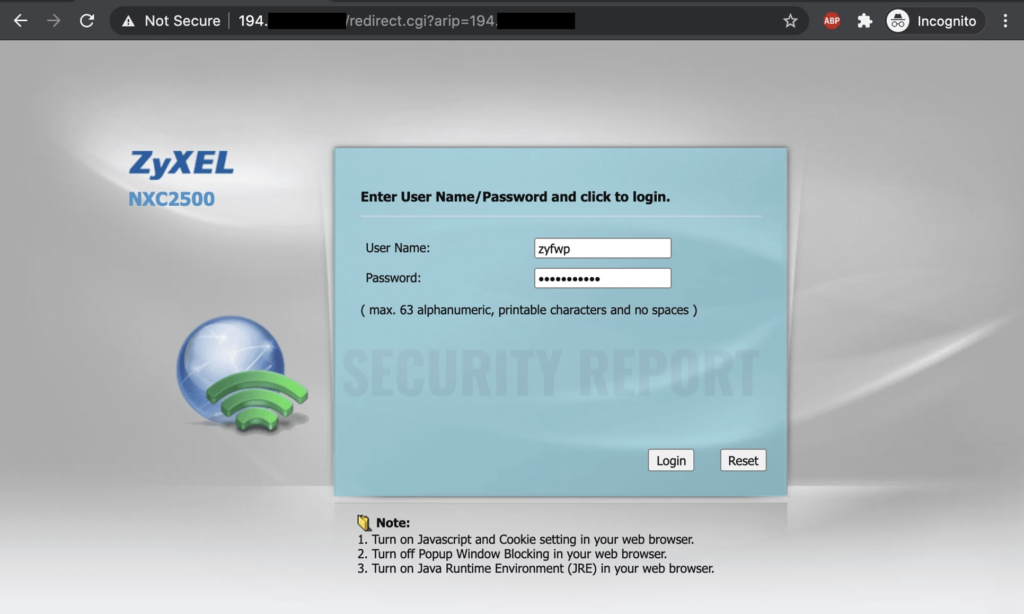
(Source: Security Report)
However, this also means, adversaries can remotely tap into the impacted Zyxel firewalls and AP controllers with administrator privileges, regardless of whether any other user accounts with strong passwords exist on the device. This hardcoded credential combination would serve as a “master key,” or a backdoor.
The bug was discovered and responsibly reported last month by security researcher Niels Teusink of EYE who released his findings, along with the username zyfwp in a blog post, but redacted the hardcoded password.
However, this week, security researcher dozer revealed the hardcoded password too: PrOw!aN_fXp
Over 100,000 exposed devices, patch now
“As SSL VPN on these devices operates on the same port as the web interface, a lot of users have exposed port 443 of these devices to the internet. Using publicly available data from Project Sonar, I was able to identify about 3,000 Zyxel USG/ATP/VPN devices in the Netherlands. Globally, more than 100,000 devices have exposed their web interface to the internet,” said Teusink in his blog post.
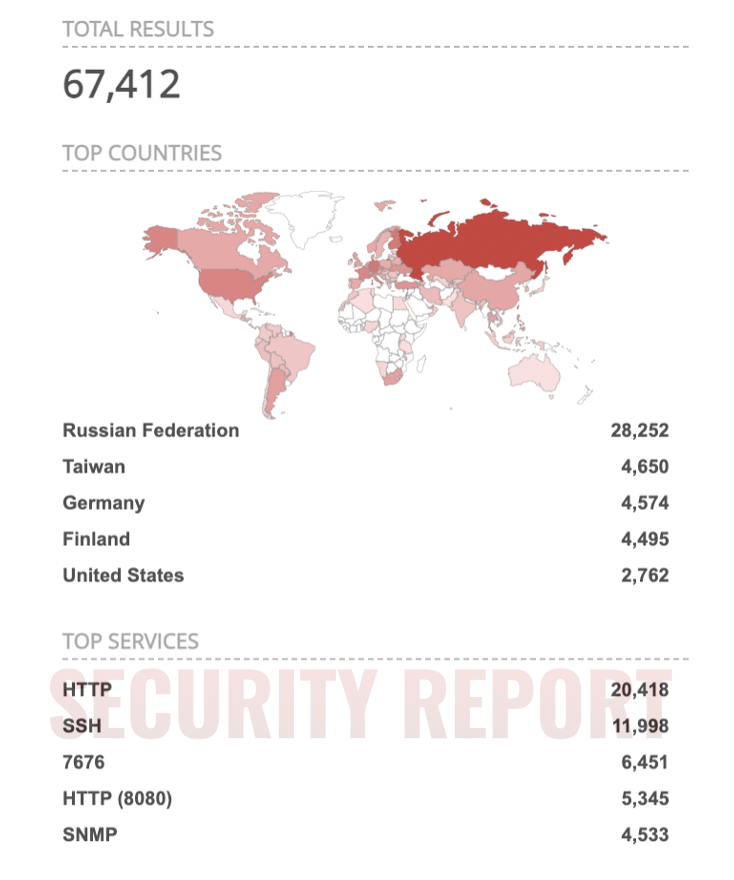
As observed by Security Report today, tens of thousands of Zyxel devices show up on IoT search engines like Shodan. While not all of these exposed devices might be vulnerable to CVE-2020-29583, the finding does point to a large Zyxel user base worldwide who could have potentially been impacted at some point by this zero-day.
Zyxel has revealed a list of vulnerable devices and patched firmware versions available that admins should upgrade their devices to.
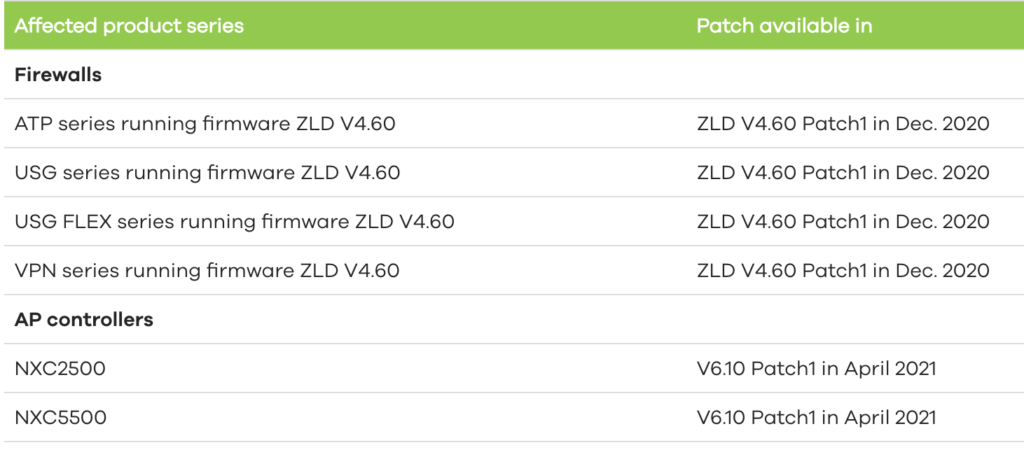
It is worth noting that automatic updates may not always be enabled on some Zyxel devices by default. Therefore, system administrators are advised to manually verify if their Zyxel hardware is impacted and apply the updates.
Revelations like these reinforce security is as strong as its weakest link and that security by obscurity doesn’t work.
A hardcoded master password in mission-critical networking devices not only renders any other admin credentials moot, but the backdoor access can also be exploited by nation-state actors to covertly conduct their surveillance activities under the radar.


