Grayhat pollutes npm, PyPI with thousands of fake supply chain dependencies
A gray hat hacker has published over 7,000 dependency confusion packages to npm and PyPI repositories, and continues to post thousands more, in real time.
A gray hat hacker has published over 7,000 dependency confusion packages to npm and PyPI repositories and continues to do so in real-time.
In the style of a vigilante, the actor is persistently publishing fake dependencies using names of real, popular components with more packages pouring in by the second as seen on PyPI.
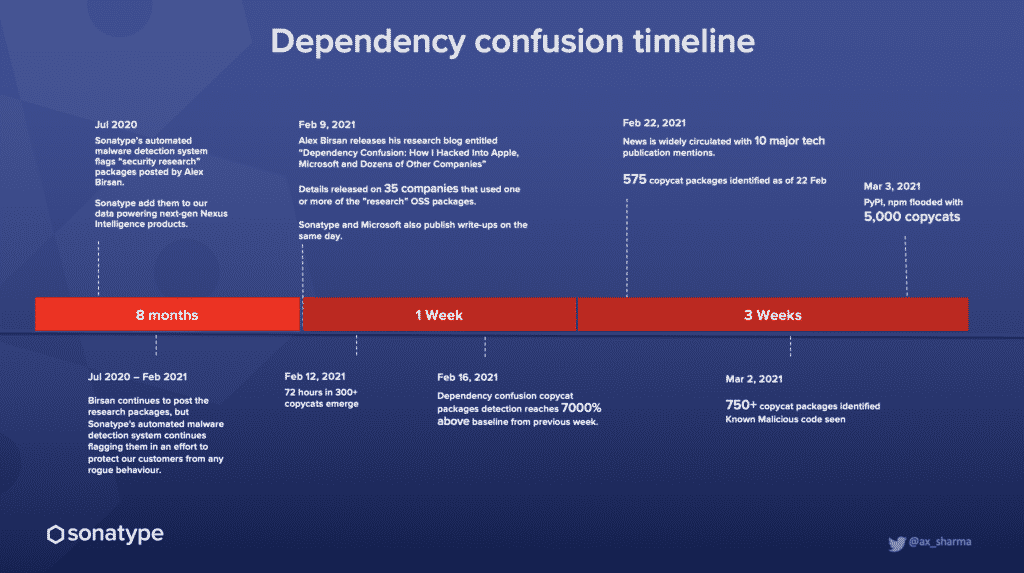
When I had reported this on the Sonatype blog yesterday, at the time, the actor had managed to spam both repos with around 5,000 packages.
(co-created with Derek Weeks, VP, Sonatype)
But, what can be observed now is a cycle of the actor persistently uploading the dependency confusion packages, with PyPI repeatedly taking them down in a “whack a mole” approach.
Most if not all of these packages have the text, “RemindSupplyChainRisks: the purpose is to make everyone pay attention to software supply chain attacks, because the risks are too great.”
These copycat packages, based off of Alex Birsan’s original ethical research packages, make an HTTP request to a Tokyo-based IP 101.32.99.28, and send the name of the copycat package in the same request to the IP.
Dependency confusion software supply chain attacks are dangerous in that they require no action on the victim’s part to get infected.
Unless specific changes are made to the development tools’ configuration to prevent the scenario of private dependencies being pulled from public open source repositories, the dependency confusion problem is likely to impact even the most secure systems.
While the actor claims to engage in the craft of flooding the repositories to demonstrate the risks to software supply chains arising from dependency confusion attacks, their way may not be all that ethical.
Fair usage policies put forth by npm and PyPI explicitly forbid unreasonably squatting names on these open-source repositories.
It is for that reason both npm and PyPI have been taking down the dependency hijacking copycats that can be seen being published on a daily basis.
As a reminder, if your project uses private, internally created npm, PyPI, RubyGems or NuGet dependencies, it would be a good idea to register their names on the open source repositories before an attacker does.
Additionally, dependency confusion checker scripts (example) and appropriate routing rules should be adopted by your repository manager products to safeguard against the dependency injection.


