Feds arrest Romanian malware actors behind CyberSeal and Dataprotector
In a joint effort, international law enforcement authorities including the FBI, Europol, and the Romanian police have arrested a hacker duo that sold malware encryption tools.
In a joint effort led by international law enforcement agencies, including the U.S. FBI, Europol, and the Romanian police, a Romanian hacker duo has been arrested for selling malware encryption tools.
These tools were used by cyberthreat actors to evade detection by making it hard for antivirus and endpoint security products to detect their malware.
“These services have been purchased by more than 1560 criminals and used for crypting several different type of malware, including Remote Access Trojans [(RATs)], information stealers, and ransomware,” stated Europol’s press release.
The duo has also been accused of selling access to a “Cyberscan service” for US$7-40, that allowed their clients to test their malware strand against antivirus programs until their malware became “fully undetectable (FUD).”
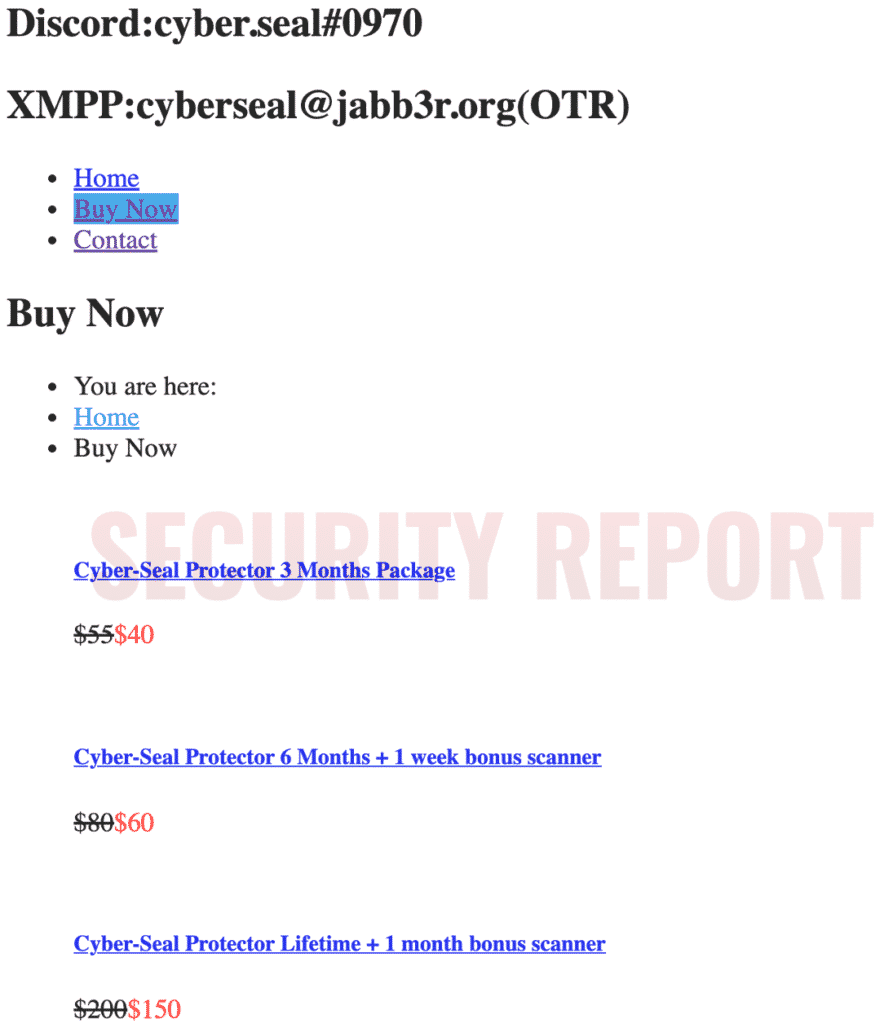
“Their clients paid between US$40 [and] US$300 for these crypting services, depending on licence conditions. Their service activity was well structured and offered regular updates and customer support to the clients,” says Europol.
While the CyberSeal site has been taken down by authorities, Security Report can confirm the site indeed had crypter (“protector”) and FUD services listed at varying prices, with a lifetime license costing US$150.
Source: Security Report News
Likewise, Security Report News observed now-shutdown domains selling DataProtector crypter access.

Source: Security Report News
Services like crypters and counter malware testing, as provided by the duo, have been offered on underground markets since at least 2010.
via Europol
Law enforcement agencies including the U.S. FBI, Romanian Police (Poliția Română, the Australian Federal Police (AFP), the Norwegian National Criminal Investigation Service (Kripos), and Europol were involved in the operation.
As a part of this investigation, in addition to arresting the hacker duo, the agencies carried out 4 house searches in Bucharest and Craiova (Romania), in addition to taking down the backend infrastructure that powered the ‘crypter’ services, in Romania, Norway, and the U.S.
Earlier this year, an Italian company was found to be selling similar “malware protector” services that aided GuLoader threat actors in conducting their malicious activities.


