Chaes malware strikes Latin American e-commerce sites
Researchers from the Cybereason Nocturnus Team have been keeping tabs on an undetected malware known as “Chaes.”
The malware discovered sometime between mid-2020 and now comprises an information stealer which works in multiple stages.
Chaes has been seen to specifically target online customers in Brazil, notably of the largest e-commerce company in Latin America, MercadoLivre.
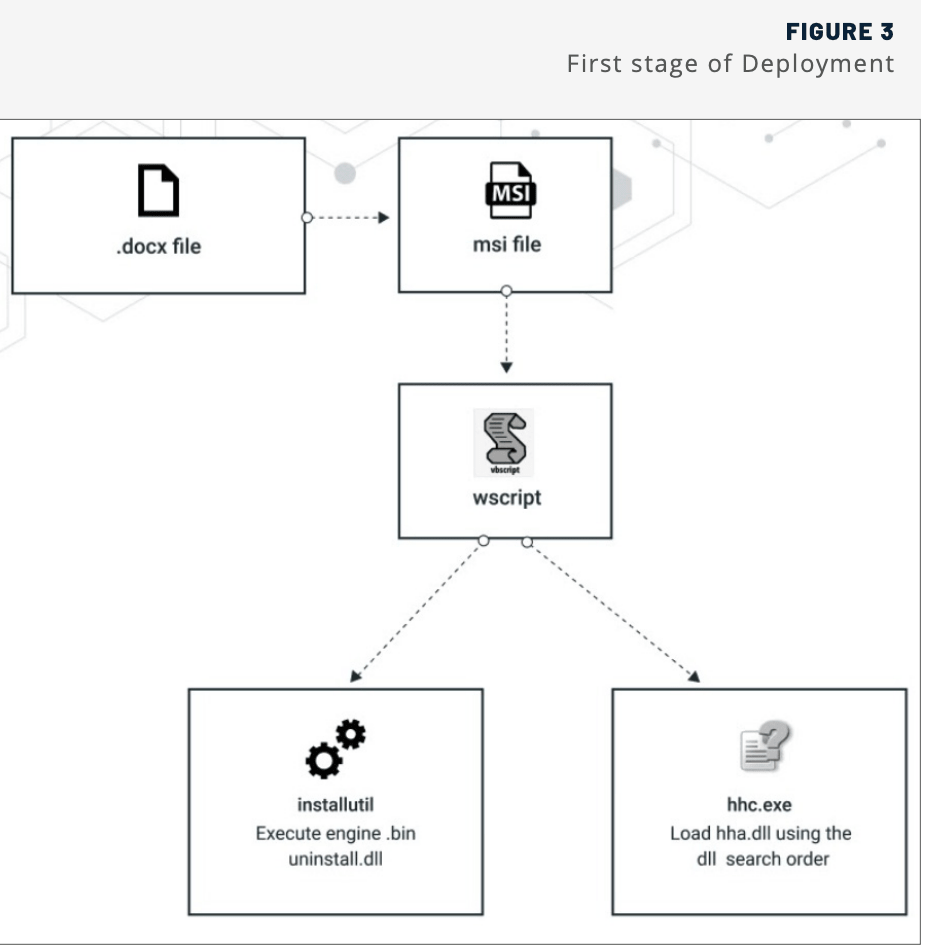
The attack begins with a phishing email containing a Microsoft Word (.docx) file.
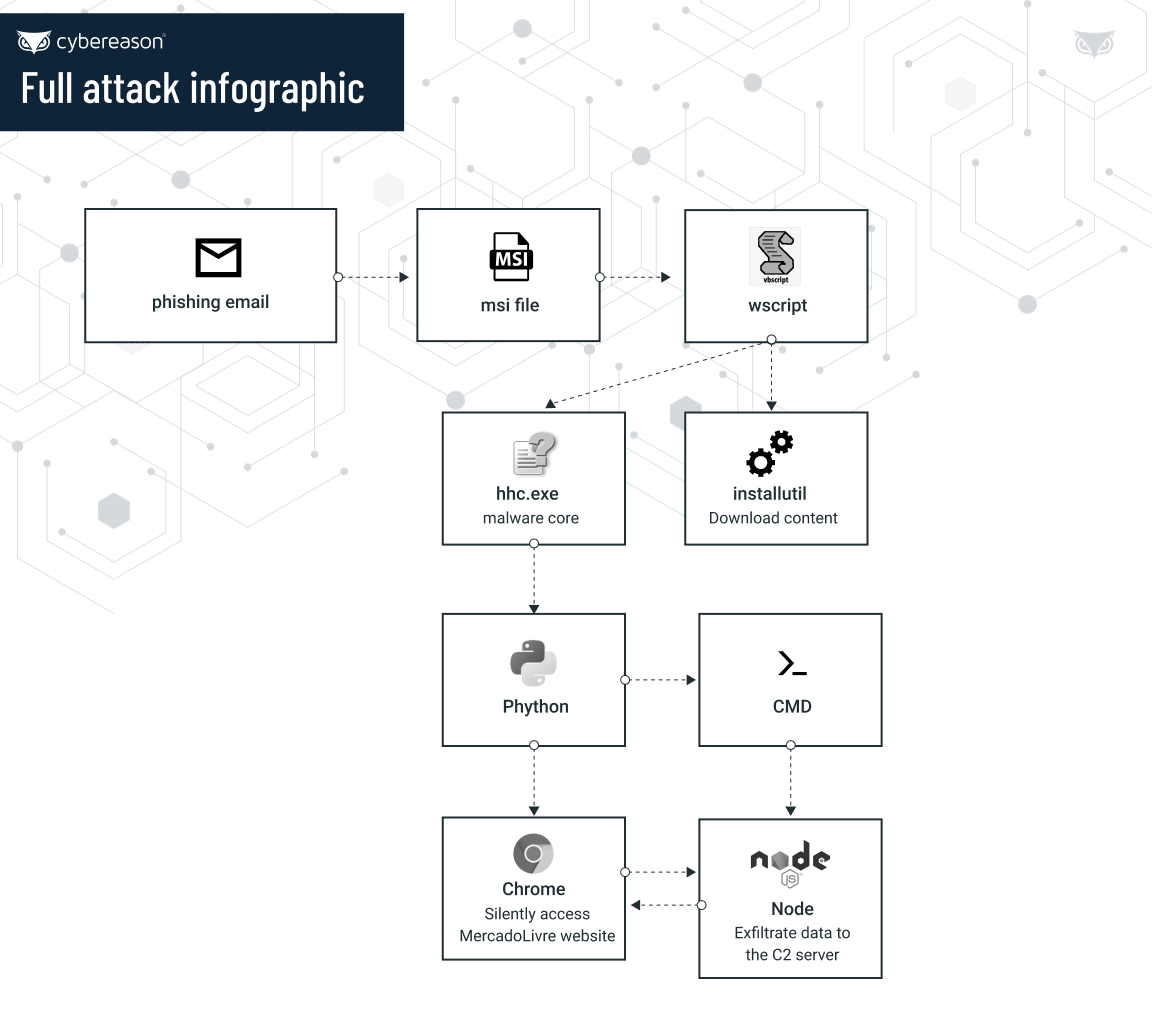
The Word document launches an MSI executable. which spawns another script. Eventually, the process workflow creates a NodeJS process and runs it via node.exe (Windows NodeJS interpreter) to exfiltrate data to the attacker’s command-and-control (C2) server.
Eli Salem, Lead Threat Hunter at Cybereason stated:
“Chaes is designed to steal sensitive information from the browser such as login credentials, credit card numbers, and other financial information from MercadoLivre website customers.”
“Chaes also takes screenshots of the infected machine, hooks and monitors the Chrome web browser to collect user information from infected hosts,” he continued.
To evade detection, the malware also employs legitimate tools such as Python, Unrar, and NodeJS. To remain stealthy, it further uses techniques like LOLBins, open-source tools, and legitimate node.js libraries.
“Threat actors put a great deal of time, resources, and effort into choosing their targets for criminal operations such as this, and a return on their investment is always top of mind. Undoubtedly, the dramatic increase in the volume of online shopping transactions has not escaped their notice, so it’s not surprising to see new and ever-more sophisticated malware variants emerging to take advantage of the current circumstances,” said Lior Div, Cybereason co-founder, and CEO.
“Individuals should be vigilant when it comes to cyber hygiene to avoid malware infections in general, and should maintain situational awareness when engaged in online shopping or banking to avoid becoming the victim attackers trying to take advantage of the pandemic and the recent increase in online financial activities.”
Cybereason’s detailed findings and a PDF report can be found on their blog.


