‘CursedGrabber’ Discord malware possibly linked to Russian and Ukrainian hackers
Newly discovered Discord malware “CursedGrabber” has possible links to Russia and Ukraine. It was found infiltrating the npm open source registry.
A new family of Discord malware has been spotted by Sonatype this week.
Known as CursedGrabber, multiple strands of this C# malware were found infecting multiple open source components in the npm registry until their takedown.
The infected components included: xpc.js, discord.app, wsbd.js, and ac-addon.
Each of these components had NodeJS code which downloaded Windows .exe binaries and launched them to run malicious code on infected machines.
Sebastián Castro, Sonatype security researcher who had analyzed the malware said, “The malware dropped by [one of the executables] lib2.exe contains advanced, multiple capabilities, such as, privilege escalation, keylogging, taking screenshots, planting backdoors, accessing webcam, etc.”
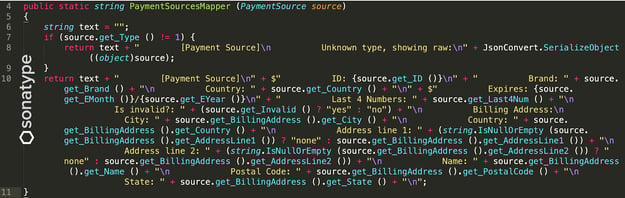
In addition to stealing a user’s Discord tokens, web browser roaming profiles, and other sensitive data, certain strands of malware family were also caught exfiltrating the user’s payment information:
While malicious component identified last week, discord.dll was not laced with CursedGrabber, it was published by the same author “luminate_” who was behind the other 4 components.
The complete research findings have been published by Sonatype.
However, I decided to dig deeper into the whereabouts of the authors behind CursedGrabber.
Note: Despite multiple indicators and clues pointing to a fact, authoritative attribution is challenging given the vast, evasive nature of the internet combined with technologies like VPNs and Tor. As such provided here are my observations and not definitive conclusions.
Possible links to Russia and Ukraine
The clues as to the origins of the CursedGrabber threat actors are revealed within the malware code and by the authors themselves.
In my independent analysis, I observed the executables dropped by the malware appear to have links to Russian and Ukrainian threat actors for the reasons outlined below.
Both legitimate npm packages, such as swearfilter, and malware published by luminate_ (aka Luminate-D and “Lann Useless“) demonstrate the author has knowledge of the Russian language.
lib2.exe in xpc.js npm malware has Russian code, as do luminate_’s legitimate packages
When decompiling CursedGrabber EXE droppers, some of them contain C# code comments crediting even more aliases, in addition to Lann.
For example, in lib.exe (present in the xpc.js package) the attribution note references 2 more aliases Assasans and Useless-Kurays:
Both of these identities have collaborated on pull requests before. Some comments in the GitHub issue (“Он принял Ислам”) are likely references to popular Russian language memes used on the forums.
‘Kurays‘ in alias Useless-Kurays comes from Russian mountainous region Kuray, whereas the user’s location listed on GitHub (“Мухосранск”) is a derogatory pun intended to describe “somewhere in Russia.”
The other alias (Assasans) claims they are based in Ukraine on GitHub.
Moreover, the contact data of some aliases could be cross-referenced with popular Russian social networking sites (e.g. VK) that pin their location to Ukraine.
Considering a third of Ukraine’s population is well-versed in the Russian language, it is likely some of the threat actors are entirely Ukrainian.
Furthermore, some malware binaries dropped by ~luminate_’s previously identified malware (such as bd.exe in the wsbd.js package ) were observed communicating with Ukrainian IPs, in addition to relying on Discord’s global infrastructure:
Although Ukraine-based, these IPs have also been listed on Russian websites and forums.
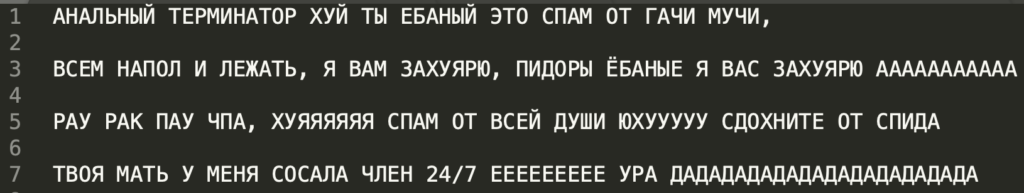
Lastly, the malicious binaries (such as lib2.exe) have Russian language notes containing expletives or “curse” words — likely why the moniker CursedGrabber was chosen by the authors.
These notes are not random swear phrases but taken from a Russian translation of an American film that had turned into a meme due to the translator’s peculiar style. The meme is popular on forums frequented by Russian and Ukrainian users.
A second Russian note contains another reference to an NSFW anime: Gachimuchi [1, 2] which, although Japanese in origin, isn’t alien to Russian-speakers.
As to why Lann and other threat actors websites are using .ml (Mali) and .tk domains for hosting their websites, there are some convincing reasons for that: .ml domains are free of cost to register, as are .tk, and would naturally lure threat actors looking for disposable, cost-free, yet valid domains.
All of these clues certainly don’t provide irrefutable evidence as to the origins of those behind CursedGrabber.
But, by the author’s own confession and attribution notes included in the malware binaries, presented here are some observations rather than conclusions.


