Cloudflare WAF bypass exploits revealed
A Cross-Site Scripting (XSS) protection bypass technique has been revealed for Cloudflare Web Application Firewall (WAF). The exploit has been publicly known since 2019 but remains unpatched.
Cloudflare Web Application Firewall (WAF) which touts itself to protect some 25 million sites remains vulnerable to rule bypasses, researchers have noted this week.
Websites protected with Cloudflare WAF intelligence typically block attackers who attempt to exploit vulnerabilities, such as SQL Injection, Cross-Site Scripting (XSS), and DoS, via common tactics and payloads.
For example, a crafted HTTP request riddled with an XSS or SQLi exploit made to a Cloudflare protected website payload would be automatically blocked by Cloudflare before it even reaches the website’s backend.
Slight modifications of generic exploit payloads, however, bypasses Cloudflare’s filters and reaches the protected website, as reported by security researchers and bug bounty hunters.
XSS filter bypass known since 2019, remains unpatched
This week, infosec researcher and bug bounty hunter Jackson Henry aka CVE-JACKSON-1337 shared how he created an SVG HTML tag, normally meant to render scalable vector graphics onto webpages to trigger a Cross-Site Scripting (XSS) proof-of-concept exploit on a Cloudflare-protected website.
While the payload shown in the researcher’s tweet is functionally equivalent to the simpler <svg onload=alert("1")> , adding a few encoded characters and leading zeros makes the payload evasive such that it flies right past Cloudflare’s WAF protections.
The researcher noted that this particular XSS bypass technique has been known publicly since at least Jun 4, 2019, when security researcher Bohdan Korzhynskyi had disclosed it.
In September 2020, Korzhynskyi reported, Cloudflare had recently downgraded certain rules in place because of which his year-old XSS protection bypass technique was working again.
WAF bypasses available for other vulnerabilities too
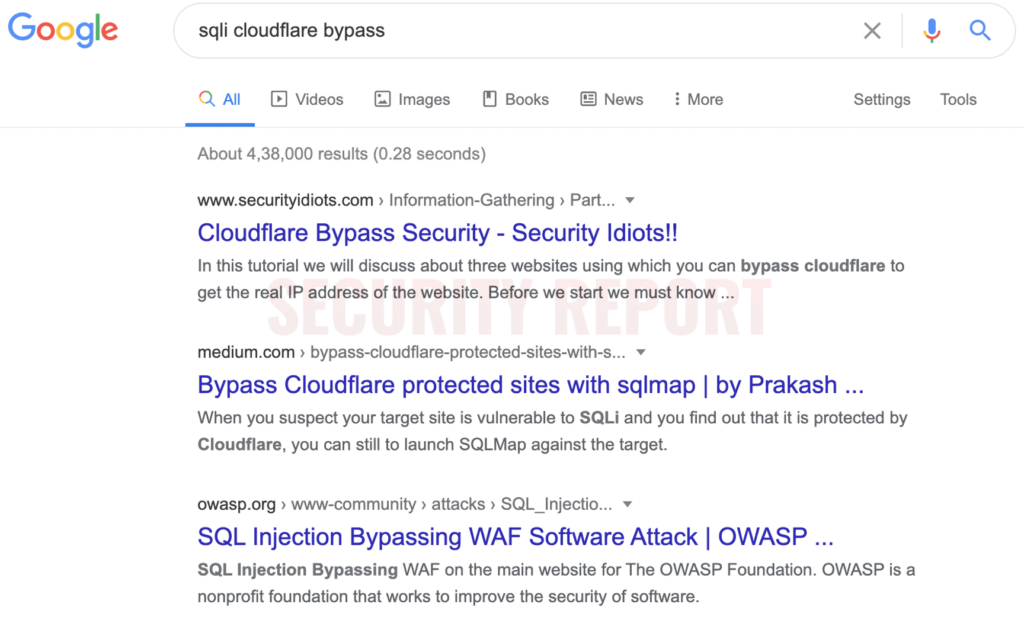
Although the researchers have demonstrated how to bypass XSS protections offered by Cloudflare, it is worth noting a simple Google search may reveal similar tactics that can be used to deliver payloads for different vulnerabilities.
Vulnerabilities like SQL Injections (SQLi), Remote Code Execution (RCE), or untrusted deserialization, if exploited, can have far more damaging consequences for websites than an XSS might.
It must be noted, protections offered by WAF are supplementary to protections built into a website’s backend. Therefore, just because an XSS payload can “pass-through” the WAF to the website’s backend, for example, does not guarantee a successful attack.
Should the website’s backend code have adequate protections against XSS, SQL Injections, and other common vulnerabilities, the attacker would not be able to succeed.
Protections offered by Cloudflare WAF and similar products are meant to be used as an additional layer of perimeter security and should not be blindly relied upon.
When asked for comment, Henry told Security Report, “Companies should not solely rely on WAFs to do the job. Industry standard protections against XSS and SQL injection should be implemented in conjunction with the chosen WAF.”
At the same time, making a WAF too restrictive and block even slightly suspicious HTTP requests may lead to false positives, and impact business operations.
Cloudflare to block the payload in next iteration of its WAF engine
Security Report reached out to Cloudflare for comment. A Cloudflare spokesperson told us:
“We value bypass notifications as they help us improve our WAF offering via our Managed Rulesets*. While bypasses do not signify a vulnerable application, being aware of these helps us block more attack vectors.”
“When we were notified of this specific XSS vector, we immediately set about fixing the bypass and provided custom rules to all customers that were concerned while we worked to close it for everyone by default.”
“To address this specific XSS vector, and add other improvements, we have been working on our next major iteration of the Firewall engine that better handles encodings. For instance, I can confirm that the payload you asked about gets blocked in the new engine:”
“The new engine is currently being tested by a group of our customers, and we expect major rollout to start early this year,” a Cloudflare spokesperson told Security Report.
*In addition to managed rulesets, the Cloudflare WAF provides the ability for customers to write and deploy custom rules to block any application specific bypasses that may not be blocked by our rulesets.
Update 5-Jan-2021: Added Cloudflare’s response.


