American Bank Systems hit by ransomware attack, full 53 GB data dump leaked
American Bank Systems (ABS), a service provider to US banks and financial institutions has suffered a ransomware attack with some of its clients’ data leaked.

American Bank Systems (ABS), a company that provides services to U.S. financial institutions and banks helping them “operate efficiently and confidently in a rapidly evolving – highly regulated – environment” has been hit by a ransomware attack this month.
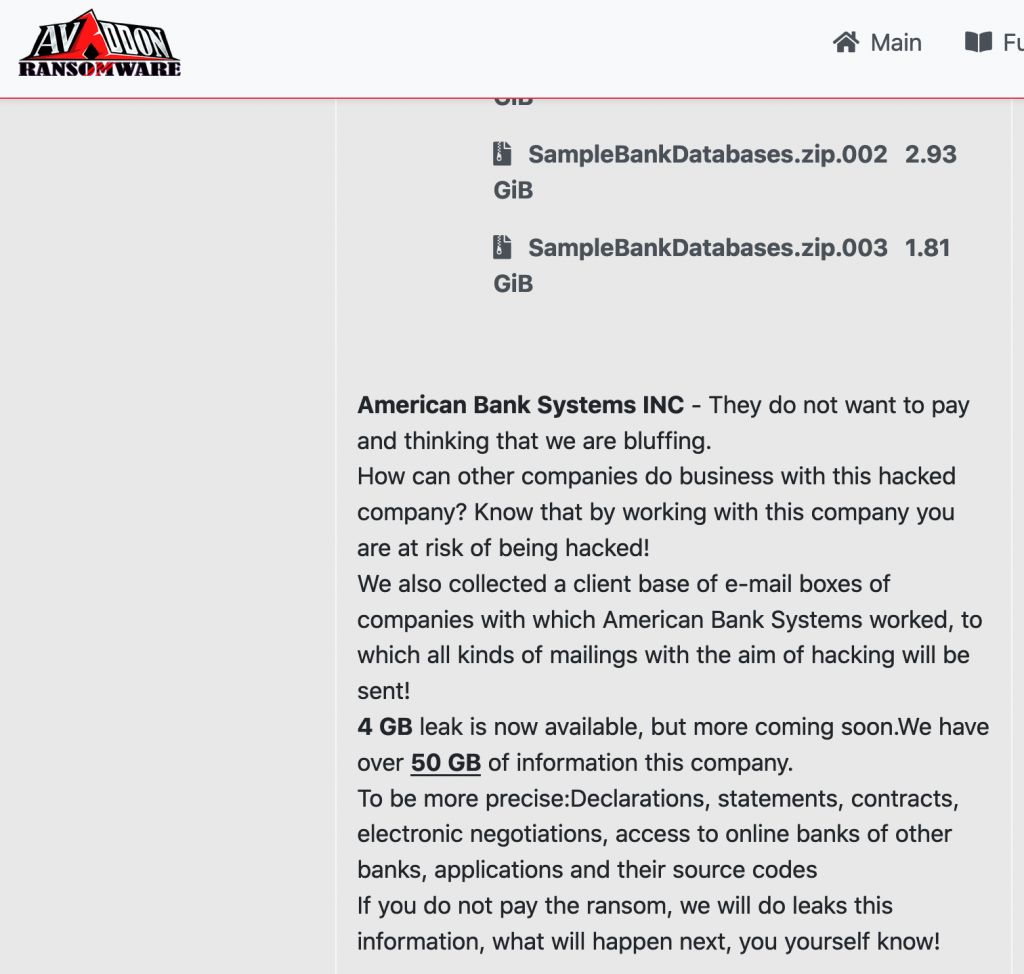
Avaddon, the ransomware group behind the attack had earlier alleged they had acquired over 50 GB of the company’s proprietary data but had leaked a partial 4 GB dump earlier this month, part of which has been analyzed by Security Report News.
It appears, this week, the threat actors have published the full 52.57 GB dump after ABS had likely refused to cooperate with Avaddon’s ransom demands.
The incident seems to have occurred sometime in or before early October, given the timestamps on the screenshots of leaked files.
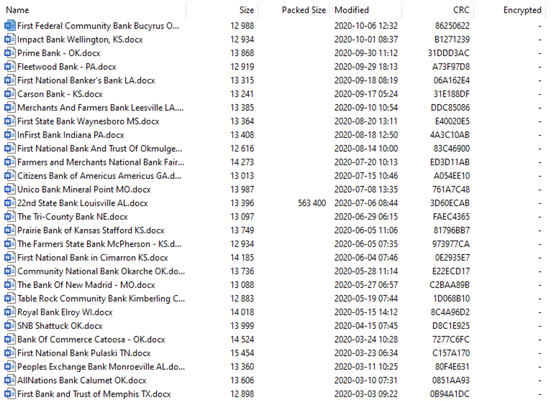
The cyberattack is concerning as ABS’ clients included multiple banking names and mortgage companies, such as First Federal Community Bank, Rio Bank, Citizens Bank of Swainsboro, First Bank & Trust, etc.
Although ABS’ clients—banks and mortgage providers, may not have been directly hit by this cyberattack, ABS does provide banking software and systems to facilitate bank processes and compliance requirements to these banks.
By breaching ABS, threat actors may have therefore gained access to their clients’ data, and further the banking customers’ data.
Data contains loan documents, emails, contracts, network shares, passwords
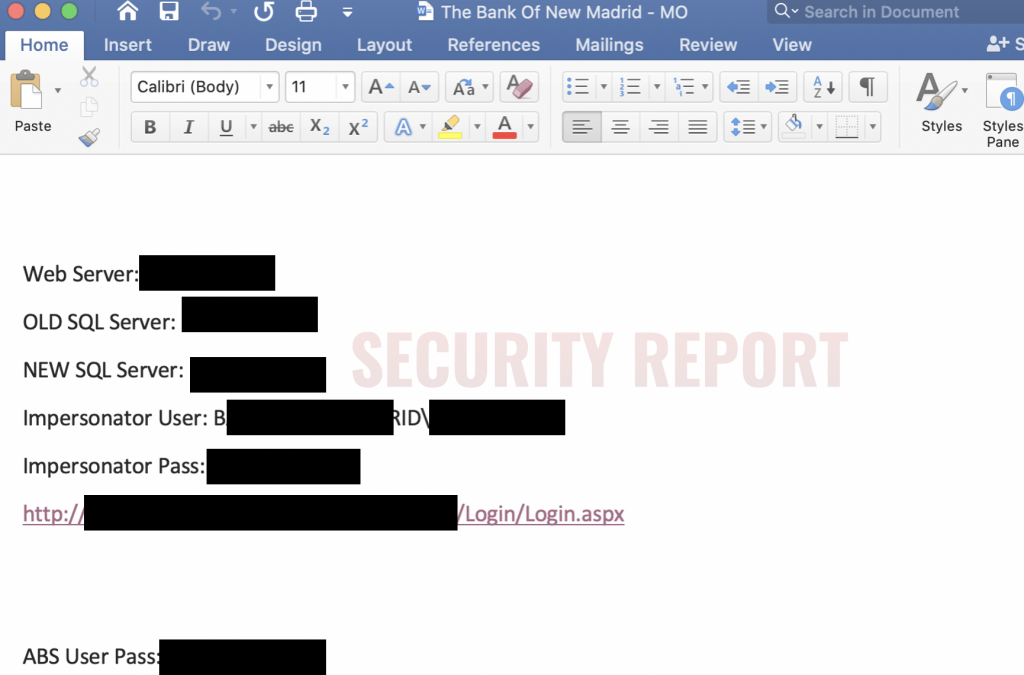
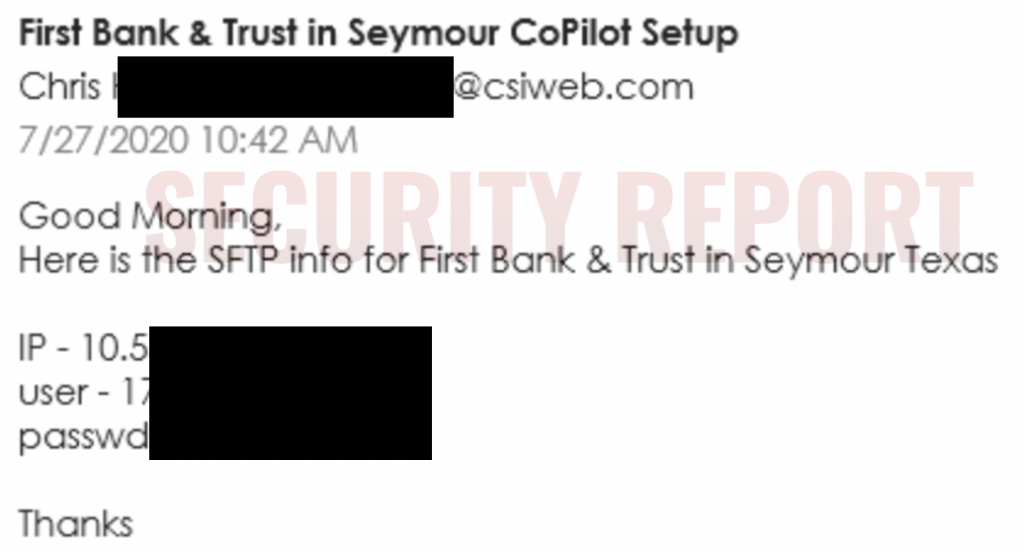
The leaked data in the dump includes files such as loan documents, business contracts, private emails, invoices, credentials for network shares, and other confidential information.
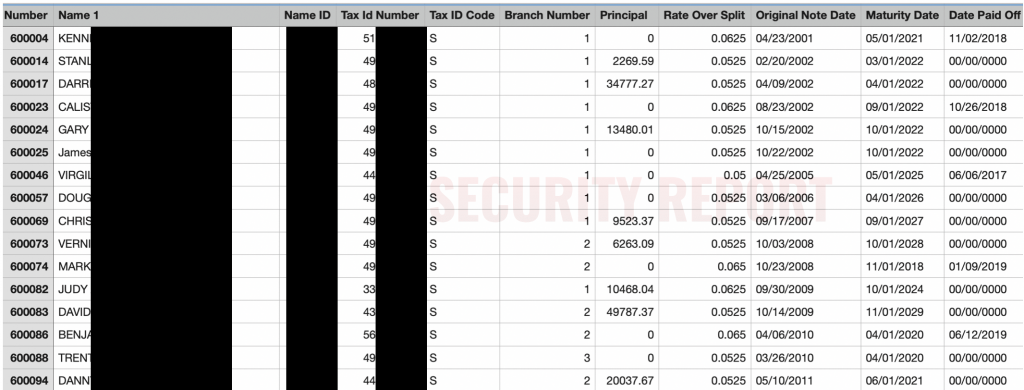
Another document, a spreadsheet shown below appears to be financial records of a bank that had used ABS’ services. This is likely how the attackers got access to the bank’s files.
In the financial document, along with personal information and loan amounts, the banking customers’ Tax ID numbers (likely Social Security Numbers) are also exposed.
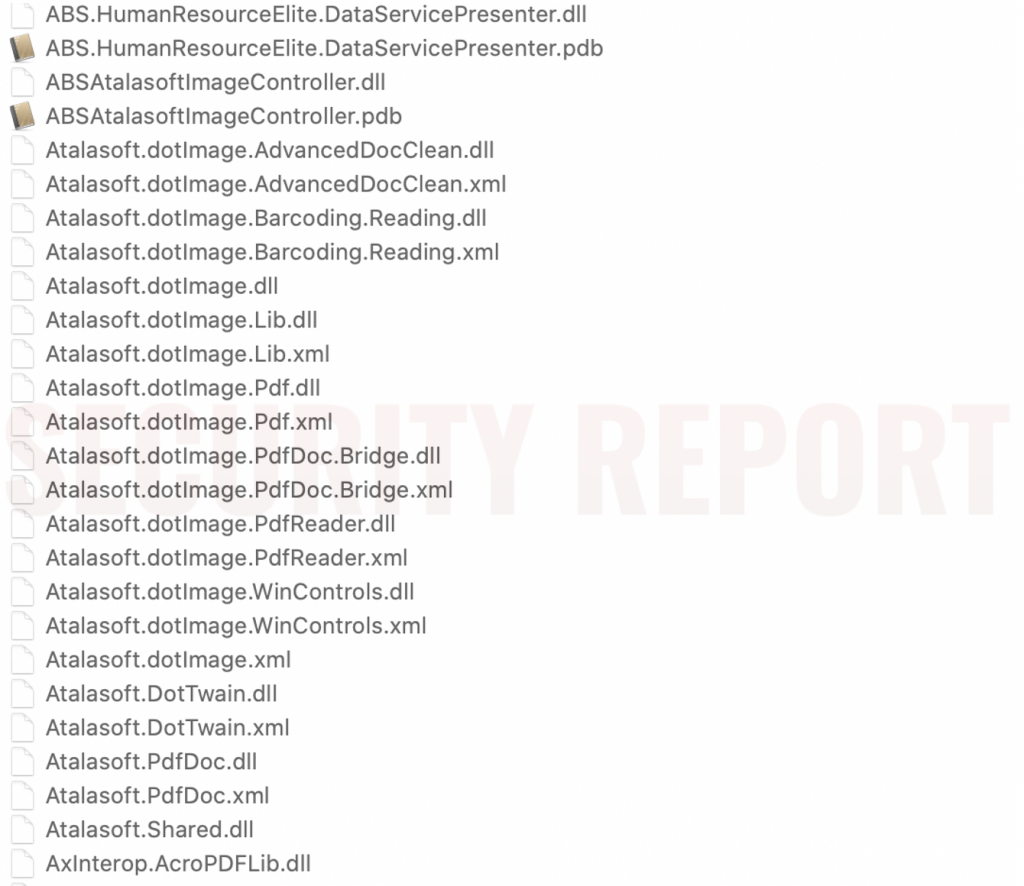
Software binaries (EXEs and DLLs) of applications used by ABS for day to day operations have also been included in the leaked dump.
Likewise, SFTP and network credentials for other banks were kept in plaintext, in Word documents that were leaked in the data dump.
Other proprietary information leaked includes what appears to be employee and customer data.
Not clear how many customers impacted
Ransomware attacks can hit any business despite having state-of-the-art security controls in place as human element remains the weakest link.
However, this incident is particularly chilling.
By breaching just one company American Bank Systems (ABS) that touts itself as providing compliance and risk management services to multiple banks, the threat actors gained access to not only ABS’ client systems (i.e. banks and financial institutions) but also got their hands on data of individuals who are customers of these banks.
It is not clear how many individual banking customers and financial organizations are impacted as a result of this breach.
Security Report had been monitoring the ransomware operators’ claims for weeks but waited to publish our findings after they were made public on Twitter:
It is also not known what steps has ABS taken to protect their systems moving forward, and those of the partner banks after this incident.
And more importantly, who is addressing the individual banking customers whose personal information has been compromised as a part of this cyberattack?
Security Report reached out to multiple ABS contacts via email for comment but we have not heard back yet.


