PoC exploits for Apache Flink Path Traversal vulnerabilities posted
This week Apache Flink has disclosed 2 path traversal vulnerabilities CVE-2020-17518 and CVE-2020-17519. Hackers have already posted Proof-of-Concept (PoC) exploits for these bugs.
This week, the Apache Flink project has disclosed two severe Path Traversal vulnerabilities in the framework that can allow attackers to both upload and retrieve arbitrary files on a vulnerable system.
Apache Flink is an open-source unified stream-processing and batch-processing framework written in Java and Scala.
Within hours of disclosure of these vulnerabilities on NVD, hackers and pentesters posted PoC exploits that can be used against vulnerable Apache Flink instances.
CVE-2020-17518: Arbitrary file upload via Path Traversal
The CVE concerns a REST handler which was introduced in Apache Flink 1.5.1 and enables file uploads to arbitrary locations on the file system of a vulnerable server.
Attackers can, for example, POST an arbitrary file along with its intended destination location to /jars/upload endpoint via an HTTP request by a crafted HTTP header shown below in an example:
Content-Disposition: form-data; name="jarfile"; filename="../../../../../../tmp/success"On successful exploitation, the attacker’s file will be uploaded to the target directory and can lead to consequences, such as overwriting existing files and achieving remote code execution.
Vulhub has posted a PoC exploit for CVE-2020-17518 that security teams can use to test their vulnerable instances.

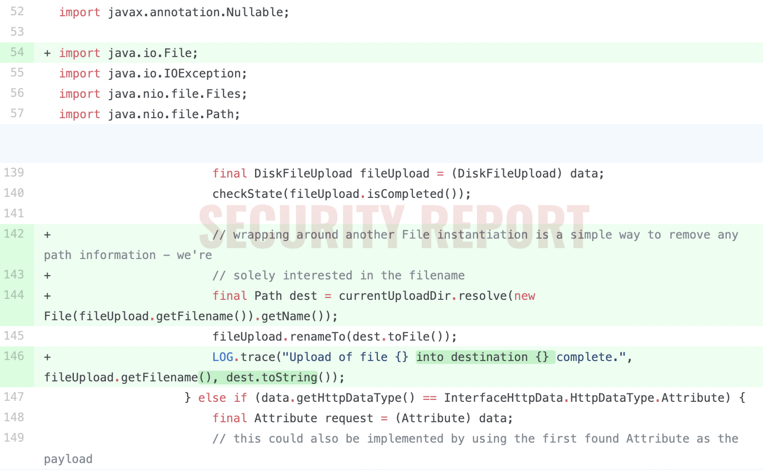
The fix made by the project, as observed by Security Report and shown below, resolves the destination path of an uploaded file in a manner that prevents Path Traversal.
CVE-2020-17519: Arbitrary file read via Path Traversal
This vulnerability was introduced in Apache Flink versions 1.11.0 and above. It allows attackers to read arbitrary files and directories on a vulnerable system.
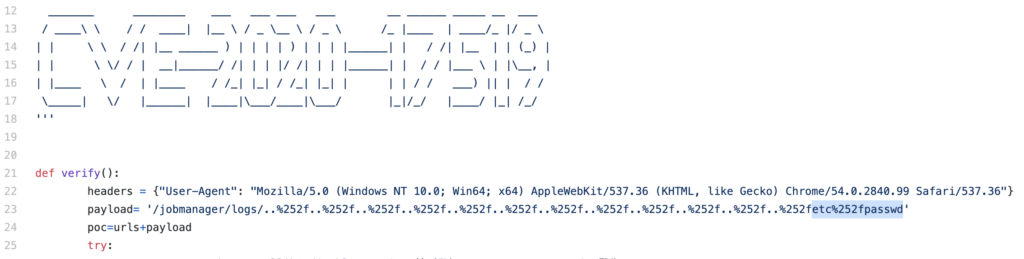
This CVE has a much simpler exploit payload as demonstrated by a PoC posted on GitHub.
The example Path Traversal payload for CVE-2020-17519 shown below attempts to retrieve the sensitive /etc/passwd file from a vulnerable server.
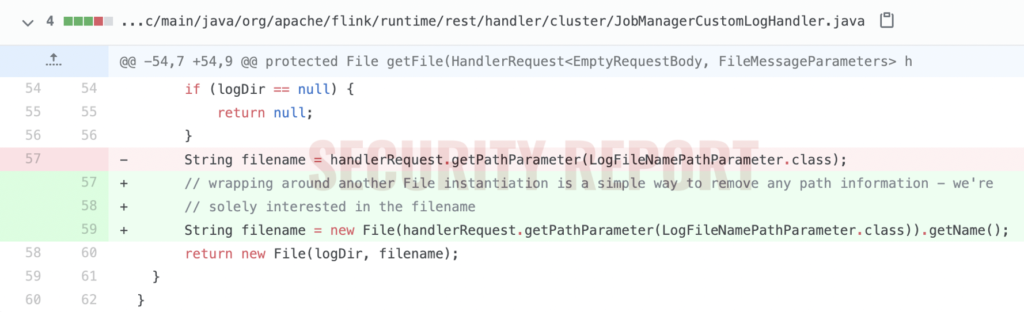
The fix made by the Apache Flink project as observed by Security Report and shown below resolves the file read vulnerability by removing direct access to a file path provided via the request handler.
Both vulnerabilities have been patched in versions 1.11.3 and above.
Flink users are advised to upgrade to fixed versions 1.11.3 or 1.12.0 of Flink, should their instances be exposed.
H/t to Jas502n and Jin Wook Kim for bringing these PoCs to light.


